CCNA 4 Final Answer
Set-1
1
Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?

Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?
The PVC to R1 must be point-to-point.
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
2
 Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
2
 Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
unplugged cable
improper LMI type
PPP negotiation failure
3
A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
Company 1 only uses microfilters at branch locations.
Company 1 has a lower volume of POTS traffic than company 2 has.
Company 2 is located farther from the service provider than company 1 is.
Company 2 shares the connection to the DSLAM with more clients than company 1 shares with.
Company 1 has a lower volume of POTS traffic than company 2 has.
Company 2 is located farther from the service provider than company 1 is.
Company 2 shares the connection to the DSLAM with more clients than company 1 shares with.
4
Refer to the exhibit. A network administrator is creating a prototype to verify the new WAN design. However, the communication between the two routers cannot be established. Based on the output of the commands, what can be done to solve the problem?Replace the serial cable .
Replace the WIC on RA.
Configure RA with a clock rate command.
Issue a no shutdown interface command on RB.

Refer to the exhibit. A network administrator is creating a prototype to verify the new WAN design. However, the communication between the two routers cannot be established. Based on the output of the commands, what can be done to solve the problem?Replace the serial cable .
Replace the WIC on RA.
Configure RA with a clock rate command.
Issue a no shutdown interface command on RB.
5
Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?The ip rip authentication key-chain command specifies exam rather than test.
The name of the keystring is not the name of the neighboring router.
The key chains are given the same name on both routers.
The passive-interface command was issued for RTA.
6
What are two main components of data confidentiality? (Choose two.)
checksum
digital certificates
encapsulation
encryption
hashing

Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?The ip rip authentication key-chain command specifies exam rather than test.
The name of the keystring is not the name of the neighboring router.
The key chains are given the same name on both routers.
The passive-interface command was issued for RTA.
6
What are two main components of data confidentiality? (Choose two.)
checksum
digital certificates
encapsulation
encryption
hashing
7
Which network component has the primary function of detecting and logging attacks made against the network?Cisco Security Agent
antivirus software scanner
intrusion detection systemintrusion prevention system
Which network component has the primary function of detecting and logging attacks made against the network?Cisco Security Agent
antivirus software scanner
intrusion detection systemintrusion prevention system
Refer to the exhibit. A network technician has been called in to resolve a problem with this network segment. The symptoms include a loss of connectivity throughout the network segment, high link utilization, and syslog messages that indicate constant MAC address relearning. What is the likely cause of these symptoms?
cable fault
faulty NIC card
IP addressing error
spanning tree problem
NAT configuration error
9
Which variable is permitted or denied by a standard access control list?
Which variable is permitted or denied by a standard access control list?
protocol type
source IP address
source MAC address
destination IP address
destination MAC address
Refer to the exhibit. To reach R2, and for configuring Frame Relay on the point-to-point interfaces shown in the graphic, which DLCI should be used in the frame-relay interface-dlci command that is issued on R1?
100
101
200
201
11
A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
Configure DHCP and static NAT.
Configure dynamic NAT for ten users.
Configure static NAT for all ten users.
Configure dynamic NAT with overload.
Refer to the exhibit. Which two actions are described by the output of the debug ip nat command? (Choose two.)
A packet from 192.168.1.2 has been translated using NAT overload.
The * indicates that the NAT translation was unsuccessful and the packet was dropped.
A packet from 192.31.7.2 has been translated by NAT and forwarded to a destination address of 198.133.219.2.
A packet from 192.31.7.2 has been sent to 198.133.219.2, which was then translated to the destination 192.168.1.2
A packet from 192.168.1.2 has been translated by NAT to a source address of 198.133.219.2 and forwarded to the destination 192.31.7.2.
Refer to the exhibit. A technician issues the show interface s0/0/0 command on R1 while troubleshooting a network problem. What two conclusions can be determined by from the output shown? (Choose two.)
The bandwidth has been set to the value of a T1 line.
This interface should be configured for PPP encapsulation.
There is no failure indicated in an OSI Layer 1 or Layer 2.
The physical connection between the two routers has failed.
The IP address of S0/0/0 is invalid, given the subnet mask being used.
14
Which Layer 2 access method separates traffic into time slots and is specified by DOCSIS for use with cable high speed Internet service?
Which Layer 2 access method separates traffic into time slots and is specified by DOCSIS for use with cable high speed Internet service?
TDMA
FDMA
CDMA
S-CDMA
Refer to the exhibit. Which data transmission technology is being represented?
TDM
PPP
HDLC
SLIP
16
Which statement is true about PAP in the authentication of a PPP session?
Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
The password is unique and random.
PAP conducts periodic password challenges.
PAP uses MD5 hashing to keep the password secure.
17
What is a common use of a TFTP server?
What is a common use of a TFTP server?
to allow access to restricted system resources
to detect attacks against a network and send logs to a management console
to provide active defense mechanisms that prevent attacks against the network
to perform IOS image and configuration uploads and downloads over the network
Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
The clock rate must be 56000.
The usernames are misconfigured.
The IP addresses are on different subnets.
The clock rate is configured on the wrong end of the link.
The CHAP passwords must be different on the two routers.
Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
19
What is the result when the command security passwords min-length 8 is entered into a router?
What is the result when the command security passwords min-length 8 is entered into a router?
All new passwords are required to be a minimum of 8 characters in length.
All current passwords are now required to be a minimum of 8 characters in length.
Enable passwords must be at least 8 characters but line passwords are unaffected.
Nothing will happen until the command service password-encryption is entered. Then all future passwords must have a minimum of 8 characters.
20
After troubleshooting a LAN, a network technician has determined that network performance has been severely impacted by the attenuation of the bit stream. Which physical layer condition led the technician to this conclusion?
After troubleshooting a LAN, a network technician has determined that network performance has been severely impacted by the attenuation of the bit stream. Which physical layer condition led the technician to this conclusion?
There is an excessive amount of EMI on the physical media.
The amplitude of the physical layer data has been significantly reduced.
There is an open conductor between the endpoints on the physical media.
The maximum allowed clock rate on the physical media has been exceeded.
21
A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
22
Which two statements are true about creating and applying access lists? (Choose two.)
Which two statements are true about creating and applying access lists? (Choose two.)
One access list per port, per protocol, per direction is permitted.
Access list entries should filter in the order from general to specific.
Statements are processed sequentially from top to bottom until a match is found.
The term “inbound” refers to traffic entering the network from the router interface where the ACL is applied.
Standard ACLs should be applied closest to the source while extended ACLs should be applied closest to the destination.
23
A network technician wants to implement SSH as the means by which a router may be managed remotely. What are two procedures that the technician should use to successfully complete this task? (Choose two.)
A network technician wants to implement SSH as the means by which a router may be managed remotely. What are two procedures that the technician should use to successfully complete this task? (Choose two.)
Configure the login banner.
Configure authentication.
Define the asymmetrical keys.
Configure the console password.
Enter the service password-encryption command.
24
Which two protocols in combination should be used to establish a link with secure authentication between a Cisco and a non-Cisco router? (Choose two.)
Which two protocols in combination should be used to establish a link with secure authentication between a Cisco and a non-Cisco router? (Choose two.)
HDLC
PPP
SLIP
PAP
CHAP
25
What will be the result of adding the command ip dhcp excluded-address 192.168.24.1 192.168.24.5 to the configuration of a local router that has been configured as a DHCP server?
What will be the result of adding the command ip dhcp excluded-address 192.168.24.1 192.168.24.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 192.168.24.1 and 192.168.24.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 192.168.24.1 and 192.168.24.5.
The DHCP server will not issue the addresses ranging from 192.168.24.1 to 192.168.24.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 192.168.24.1 and 192.168.24.5.
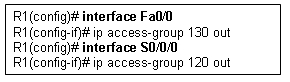
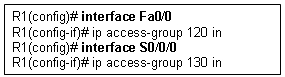
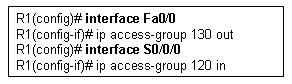
Refer to the exhibit. The network administrator creates a standard access control list to prohibit traffic from the 192.168.1.0/24 network from reaching the Internet. The access list must still permit the 192.168.1.0/24 network access to the 192.168.2.0 network. On which router interface and in which direction should the access control list be applied?
interface Fa0/0, inbound
interface Fa0/0, outbound
interface S0/0/0, inbound
interface S0/0/0, outbound
Refer to the exhibit. Which statement is true about the Frame Relay connection?
The Frame Relay connection is in the process of negotiation.
A congestion control mechanism is enabled on the Frame Relay connection.
The “ACTIVE” status of the Frame Relay connection indicates that the network is experiencing congestion.
Only control FECN and BECN bits are sent over the Frame Relay connection. No data traffic traverses the link.
Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
29
An administrator attempts to telnet into a remote device and receives the error “Password required but none set”. How can the administrator resolve this issue?
An administrator attempts to telnet into a remote device and receives the error “Password required but none set”. How can the administrator resolve this issue?
Set the enable secret command on the remote router.
Set the login command on the vty lines on the remote router.
Set the password command on the vty lines on the remote router.
Enable the service password-encryption command on the remote router.
Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem?
The default gateway is in the wrong subnet.
STP has blocked the port that PC1 is connected to.
Port Fa0/2 on S2 is assigned to the wrong VLAN.
S2 has the wrong IP address assigned to the VLAN30 interface.
31
Which additional functionality is available on an interface when the encapsulation is changed from HDLC to PPP?
Which additional functionality is available on an interface when the encapsulation is changed from HDLC to PPP?
flow control
error control
authentication
synchronous communication
Refer to the exhibit. A technician is teaching a trainee to interpret the results of various Frame Relay troubleshooting commands. What conclusion can be drawn from the output that is shown?
Neighboring routers should use DLCI 177 to reach the Branch router.
DLCI 177 will be used to identify all broadcasts that are sent out the Branch router.
The Branch router has the address 192.168.3.1 configured for the S0/0/0 interface.
To reach 192.168.3.1, the Branch router will use the virtual circuit that is identified by DLCI 177.
Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses?
/19
/20
/21
/22
/23
/24
34
A network administrator uses the 3DES algorithm to encrypt traffic that crosses a VPN. Which VPN characteristic is being configured?
A network administrator uses the 3DES algorithm to encrypt traffic that crosses a VPN. Which VPN characteristic is being configured?
authentication
authorization
data integrity
data confidentiality
35
Which statement is true about wildcard masks?
Which statement is true about wildcard masks?
A wildcard mask must be created by inverting the subnet mask.
A wildcard mask performs the same function as a subnet mask.
A wildcard mask of 0.0.0.0 means the address should match exactly.
A wildcard mask uses a “1″ to identify IP address bits that must be checked.
Refer to the exhibit. What statement is true about the core router devices?
They use multiport internetworking devices to switch traffic such as Frame Relay, ATM, or X.25 over the WAN.
They provide internetworking and WAN access interface ports that are used to connect to the service provider network.
They provide termination for the digital signal and ensure connection integrity through error correction and line monitoring.
They support multiple telecommunications interfaces of the highest speed and are able to forward IP packets at full speed on all of those interfaces.
37
When NAT is in use, what is used to determine the addresses that can be translated on a Cisco router?
When NAT is in use, what is used to determine the addresses that can be translated on a Cisco router?
access control list
routing protocol
inbound interface
ARP cache
38
A network administrator is instructing a technician on best practices for applying ACLs. Which suggestion should the administrator provide?
A network administrator is instructing a technician on best practices for applying ACLs. Which suggestion should the administrator provide?
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied closest to the core layer.
ACLs applied to outbound interfaces are the most efficient.
Extended ACLs should be applied closest to the source that is specified by the ACL.
39
Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
172.16.0.0 0.0.0.1
172.16.0.0 0.0.0.3
172.16.0.0 0.0.0.7
172.16.0.0 255.255.255.252
40
When configuring a Frame Relay connection, what is the purpose of Inverse ARP?
When configuring a Frame Relay connection, what is the purpose of Inverse ARP?
to assign a DLCI to a remote peer
to disable peer requests from determining local Layer 3 addresses
to negotiate LMI encapsulations between local and remote Frame Relay peers
to create a mapping of DLCI to Layer 3 addresses that belong to remote peers
41
Which security solution has the responsibility of monitoring suspicious processes that are running on a host and that might indicate infection of Trojan horse applications?
Which security solution has the responsibility of monitoring suspicious processes that are running on a host and that might indicate infection of Trojan horse applications?
antivirus application
operating system patches
intrusion prevention system
Cisco Adaptive Security Appliance
42
What is the function of an intrusion detection system on a network?
What is the function of an intrusion detection system on a network?
to restrict access to only authorized users
to detect attacks against a network and send logs to a management console
to prevents attack against the network and provide active defense mechanisms
to detect and prevent most viruses and many Trojan horse applications from spreading in the network
43
Which statement about a VPN is true?
Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
44
An administrator learns of an e-mail that has been received by a number of users in the company. This e-mail appears to come from the office of the administrator. The e-mail asks the users to confirm their account and password information. Which type of security threat does this e-mail represent?
An administrator learns of an e-mail that has been received by a number of users in the company. This e-mail appears to come from the office of the administrator. The e-mail asks the users to confirm their account and password information. Which type of security threat does this e-mail represent?
cracking
phishing
phreaking
spamming
Refer to the exhibit. An ACL called Managers already exists on this router. What happens if the network administrator issues the commands as shown in the exhibit?
The commands are added to the end of the existing ACL.
The existing Managers ACL will be overwritten by the new ACL.
The router will output an error message and no changes will be made.
A duplicate Managers ACL will be created that will contain only the new commands.
46
Which encapsulation protocol when deployed on a Cisco router over a serial interface is only compatible with another Cisco router?
Which encapsulation protocol when deployed on a Cisco router over a serial interface is only compatible with another Cisco router?
PPP
SLIP
HDLC
Frame Relay
47
What name is given to the location where a customer network interfaces with a network that is owned by another organization?
What name is given to the location where a customer network interfaces with a network that is owned by another organization?
CPE
DCE
local loop
demarcation point
Refer to the exhibit. Which option displays the correct ACL that would need to be applied inbound on the S0/0/0 interface on R2 in order to permit any type of network traffic and block all FTP traffic coming from hosts on the 172.16.10.0/24 network going to the Internet?

49
Refer to the exhibit. A network administrator is trying to backup the IOS software on R1 to the TFTP server. He receives the error message that is shown in the exhibit, and cannot ping the TFTP server from R1. What is an action that can help to isolate this problem?
Use correct source file name in the command.
Verify that the TFTP server software is running.
Make sure that there is enough room on the TFTP server for the backup.
Check that R1 has a route to the network where the TFTP server resides.
50
A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
51
Which characteristic of VPN technology prevents the contents of data communications from being read by unauthorized parties?
Which characteristic of VPN technology prevents the contents of data communications from being read by unauthorized parties?
QoS
latency
reliability
confidentiality
52
Which configuration on the vty lines provides the best security measure for network administrators to remotely access the core routers at headquarters?

Which configuration on the vty lines provides the best security measure for network administrators to remotely access the core routers at headquarters?


Exam Results – EWAN Final Exam – CCNA Exploration: Accessing the WAN – Version 4.0
Date Exam was Taken: 16/05/2011
Domain Knowledge – Weighted Score
Max Points: 100
Earned Points: 90
Percentage: 90.0%
Max Points: 100
Earned Points: 90
Percentage: 90.0%
Personalized Feedback has been generated based on your responses to this exam. Click Here to view your Personalized Feedback
Domain Knowledge – Binary Score
Max Points: 50
Earned Points: 44
Percentage: 88.0
Domain Knowledge – Binary Score
Max Points: 50
Earned Points: 44
Percentage: 88.0
Set-2
1. What are two main components of data confidentiality? (Choose two.)
checksum
digital certificates
encapsulation
encryption
hashing
2. Which network component has the primary function of detecting and logging attacks made against the network?
Cisco Security Agent
antivirus software scanner
intrusion detection system
intrusion prevention system
3.
Refer to the exhibit. A network administrator has issued the commands that are shown on Router1 and Router2. A later review of the routing tables reveals that neither router is learning the LAN network of the neighbor router. What is most likely the problem with the RIPng configuration?
The serial interfaces are in different subnets.
The RIPng process is not enabled on interfaces.
The RIPng network command is not configured.
The RIPng processes do not match between Router1 and Router2.
4. Which three guidelines would help contribute to creating a strong password policy? (Choose three.)
Once a good password is created, do not change it.
Deliberately misspell words when creating passwords.
Create passwords that are at least 8 characters in length.
Use combinations of upper case, lower case, and special characters.
Write passwords in locations that can be easily retrieved to avoid being locked out.
Use long words found in the dictionary to make passwords that are easy to remember.
5.
Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
The clock rate must be 56000.
The usernames are misconfigured.
The IP addresses are on different subnets.
The clock rate is configured on the wrong end of the link.
The CHAP passwords must be different on the two routers.
Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
6.
Refer to the exhibit. Headquarters is connected through the Internet to branch office A and branch office B. Which WAN technology would be best suited to provide secure connectivity between headquarters and both branch offices?
ATM
VPN
ISDN
Frame Relay
broadband DSL
7. Which combination of authentication and Layer 2 protocol should be used to establish a link between a Cisco and a non-Cisco router without sending authentication information in plain text?
CHAP and HDLC
CHAP and PPP
PAP and HDLC
PAP and PPP
8. A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
Company 2 downloads larger files than company 1 downloads.
Company 2 must share the connection to the DSLAM with more clients than company 1 shares.
Company 1 is closer to the service provider than is company 2.
Company 1 has a lower volume of POTS traffic than company 2 has.
9.
Refer to the exhibit. The network administrator creates a standard access control list to prohibit traffic from the 192.168.1.0/24 network from reaching the Internet. The access list must still permit the 192.168.1.0/24 network access to the 192.168.2.0 network. On which router interface and in which direction should the access control list be applied?
interface Fa0/0, inbound
interface Fa0/0, outbound
interface S0/0/0, inbound
interface S0/0/0, outbound
10. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology.
Incorrect IPv4 addresses are entered on the router interfaces.
RIPng is incompatible with dual-stack technology.
IPv4 is incompatible with RIPng.
11.
Refer to the exhibit. A network administrator is trying to backup the IOS software on R1 to the TFTP server. He receives the error message that is shown in the exhibit, and cannot ping the TFTP server from R1. What is an action that can help to isolate this problem?
Use correct source file name in the command.
Verify that the TFTP server software is running.
Make sure that there is enough room on the TFTP server for the backup.
Check that R1 has a route to the network where the TFTP server resides.
12.
Refer to the exhibit. Partial results of the show access-lists and show ip interface FastEthernet 0/1 commands for router Router1 are shown. There are no other ACLs in effect. Host A is unable to telnet to host B. Which action will correct the problem but still restrict other traffic between the two networks?
Apply the ACL in the inbound direction.
Apply the ACL on the FastEthernet 0/0 interface.
Reverse the order of the TCP protocol statements in the ACL.
Modify the second entry in the list to permit tcp host 172.16.10.10 any eq telnet .
13. What component of VPN technology combines message text with a key to make the message unreadable by unauthorized receivers?
message hash
user password
RSA signature
encryption algorithm
14. Which variable is permitted or denied by a standard access control list?
protocol type
source IP address
source MAC address
destination IP address
destination MAC address
15.
Refer to the exhibit. An ACL called Managers already exists on this router. What happens if the network administrator issues the commands as shown in the exhibit?
The new ACL overwrites the existing ACL.
The network administrator will receive an error message.
The existing ACL is modified to include the new command.
A second Managers ACL is created that contains only the new command.
16.
Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 have not received any RIP routing updates. What will fix the issue?
Enable RIP authentication on R2.
Issue the ip directed-broadcast command on R2.
Change the subnet masks to 10.11.12.0/8 and 172.16.40.0/16 on R2.
Enable CDP on R2 so that the other routers will receive routing updates.
17. What name is given to the location where a customer network interfaces with a network that is owned by another organization?
CPE
DCE
local loop
demarcation point
18.
Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the Orlando router to the DC router?
DLCI 123
DLCI 321
10.10.10.25
10.10.10.26
MAC address of the DC router
19.
Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
20. What will be the result of adding the command ip dhcp excluded-address 10.10.4.1 10.10.4.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 10.10.4.1 and 10.10.4.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 10.10.4.1 and 10.10.4.5.
The DHCP server will not issue the addresses ranging from 10.10.4.1 to 10.10.4.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 10.10.4.1 and 10.10.4.5.
21. What functionality do access control lists provide when implementing dynamic NAT on a Cisco router?
which addresses are allowed to be accessed from the inside network
which addresses are allowed out of the router
which addresses are assigned to a NAT pool
which addresses are to be translated
22. Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
23.
Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
24. An administrator is unable to receive e-mail. While troubleshooting the problem, the administrator is able to ping the local mail server IP address successfully from a remote network and can also successfully ping using the mail server name. At which layer of the OSI model is the problem most likely to be found?
physical layer
network layer
data link layer
application layer
25. Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
ATM
Frame Relay
HDLC
PPP
SDLC
26. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
27. Which statement accurately describes a role that is played in establishing a WAN connection?
ISDN and ATM are circuit-switched technologies that are used to establish on demand a path through the service provider network.
Data link layer protocols like PPP and HDLC define how data is encapsulated for transmission across a WAN link.
A packet-switching network establishes a dedicated circuit between nodes for the duration of the communication session.
Frame Relay switches are normally considered to be customer premises equipment (CPE) and are maintained by local administrators.
28.
Refer to the exhibit. What is the meaning of the term dynamic in the output of the command?
The bandwidth capability of the interface increases and decreases automatically based on BECNs.
The Serial0/0/1 interface acquired 172.16.3.1 from a DHCP server.
The mapping between DLCI 100 and 172.16.3.1 was learned through Inverse ARP.
DLCI 100 will automatically adapt to changes in the Frame Relay cloud.
29. What is an accurate description of CHAP when used with PPP on a serial connection between two routers?
A username and password are sent to the peer router, which replies with an accept or reject message.
A username and password are sent to the peer router. If these match the configuration in the peer, the peer in turn provides a username and password to the initiating router.
A challenge message is sent to the peer router, which responds with its username and a calculated value based on a shared secret. This value is then compared by the challenger to its own calculations.
An encrypted password is sent to the peer router, which decrypts it and compares it to a shared secret. If the decrypted passwords match, the peer sends the encrypted password back to the initiating router.
30. Which technology is used to dynamically map next hop, network layer addresses to virtual circuits in a Frame Relay network?
Inverse ARP
LMI
DLCI
31.
Refer to the exhibit. A network administrator is trying to connect R1 remotely to make configuration changes. Based on the exhibited command output, what will be the result when attempting to connect to R1?
failure to connect due to Telnet not being enabled
failure to connect due to incomplete configuration for Telnet
a successful connection and ability to make configuration changes
a successful connection but inability to make configuration changes because of the absence of an enable secret password
32. A DHCP server is configured with a block of excluded addresses. What two devices would be assigned static addresses from the excluded address range? (Choose two.)
a protocol analyzer
DNS server for the network
network printer that is used by many different users
a laptop that will get a different address each time it boots up
33.
Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses?
/19
/20
/21
/22
/23
/24
34. Compared with IDS systems, what can IPS systems do to provide further protection of computer systems?
detect potential attacks
stop the detected attack from executing
update OS patches for computer systems
scan computer systems for viruses and spyware
35. A company has its headquarters office in Dallas and five branch offices located in New York, Chicago, Los Angeles, Seattle, and Atlanta. WAN links are used for communications among offices in six sites. In planning the WAN links, the network designer is given two requirements: (1) minimize cost and (2) provide a certain level of WAN link reliability with redundant links. Which topology should the network designer recommend?
star
full mesh
hierarchical
partial mesh
36.
Refer to the exhibit. Every time the administrator reboots this router, the boot process ends in setup mode. What is a possible problem?
There is insufficient RAM for the IOS to load on this router.
A password recovery process should be done on this router.
The bootstrap version and the version of the IOS are different.
The IOS image is damaged and must be reloaded using tftpdnld.
The configuration register is set to ignore the startup configuration.
37. An administrator issues the command show interfaces s0/1/0 on a router that is configured for Frame Relay. Which console output may indicate an LMI mismatch?
Serial0/1/0 is administratively down
Serial0/1/0 is up, line protocol is up
Serial0/1/0 is up, line protocol is down
Serial0/1/0 is down, line protocol is down
38.Refer to the exhibit. Users who are connected to R1 report that they are unable to establish connectivity to the users who are connected to router R2. A network administrator tests the link with the debug ppp authentication command. Based on the output shown, which statement correctly defines the problem on the link?
R1 uses PAP as a method of authentication, and R2 uses CHAP.
R1 uses CHAP as a method of authentication, and R2 uses PAP.
R1 uses an incorrect user name or password for CHAP authentication.
R2 uses an incorrect user name or password for PAP authentication.
39. Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
172.16.0.0 0.0.0.1
172.16.0.0 0.0.0.3
172.16.0.0 0.0.0.7
172.16.0.0 255.255.255.252
40. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
41.
Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to the web server. What is the destination IP address of the return packet from the web server?
10.1.1.2:1234
172.30.20.1:1234
172.30.20.1:3333
192.168.1.2:80
42. What function does LCP perform in the establishment of a PPP session?
LCP brings the network layer protocols up and down.
It carries packets from several network layer protocols.
It encapsulates and negotiates options for IP and IPX.
It negotiates and sets up control options on the WAN data link.
43. An employee of XYZ corporation will begin working from home. The employee has a choice of DSL or cable technology for WAN connectivity. Which connectivity characteristic is accurately described?
Cable transfer rates are dependent on the length of the local loop.
DSL provides a high-speed connection over existing copper phone wires.
DSL download speeds are affected by high usage in the area.
DSL service shares the same frequency range as voice calls.
Cable connectivity usually requires new fiber installed for the local loop.
44. Which option represents a best practice for applying ACLs?
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied inside the core layer.
ACLs applied to outbound interfaces use fewer router resources.
Extended ACLs should be applied closest to the source that is specified by the ACL.
45. While troubleshooting a problem with an e-mail server, an administrator observes that the switch port used by the server shows “up, line protocol up”. The administrator cannot ping the server. At which layer of the OSI model is the problem most likely to be found?
application layer
network layer
data link layer
physical layer
46. Which two configurations must be completed before an RSA key can be generated on a router? (Choose two.)
a hostname
a domain name
the SSH version
the SSH timeouts
local authentication on the VTY lines
47. What type of ACL can be used to force a user to authenticate to the router before accessing a network?
standard
dynamic
reflexive
time-based
48. What is the result when the command security passwords min-length 8 is entered into a router?
All new passwords are required to be a minimum of 8 characters in length.
All current passwords are now required to be a minimum of 8 characters in length.
Enable passwords must be at least 8 characters but line passwords are unaffected.
Nothing will happen until the command service password-encryption is entered. Then all future passwords must have a minimum of 8 characters.
49. Because of a remote-procedure call failure, a user is unable to access an NFS server. At what layer of the TCP/IP model does this problem occur?
network layer
data link layer
physical layer
application layer
50. What is the result when the command permit tcp 10.25.132.0 0.0.0.255 any eq smtp is added to a named access control list and applied on the inbound interface of a router?
TCP traffic with a destination to the 10.25.132.0/24 is permitted.
Only Telnet traffic is permitted to the 10.24.132.0/24 network
Ttraffic from 10.25.132.0/24 is permitted to anywhere on using any port.
Traffic using port 25 from the 10.25.132.0/24 is permitted to all destinations.
—————
1.Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
2. Refer to the exhibit. A network administrator is tasked with completing the Frame Relay topology that interconnects two remote sites. How should the point-to-point subinterfaces be configured on HQ to complete the topology?
frame-relay interface-dlci 103 on Serial 0/0/0.1
frame-relay interface-dlci 203 on Serial 0/0/0.2
frame-relay interface-dlci 301 on Serial 0/0/0.1
frame-relay interface-dlci 302 on Serial 0/0/0.2
frame-relay map ip 192.168.1.1 103 broadcast on Serial 0/0/0.1
frame-relay map ip 192.168.2.2 203 broadcast on Serial 0/0/0.2
frame-relay map ip 192.168.1.1 301 broadcast on Serial 0/0/0.1
frame-relay map ip 192.168.2.2 302 broadcast on Serial 0/0/0.2
3. Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
ATM
Frame Relay
HDLC
PPP
SDLC
4. Refer to the exhibit. Company ABC expanded its business and recently opened a new branch office in another country. IPv6 addresses have been used for the company network. The data servers Server1 and Server2 run applications which require end-to-end functionality, with unmodified packets that are forwarded from the source to the destination. The edge routers R1 and R2 support dual stack configuration. What solution should be deployed at the edge of the company network in order to successfully interconnect both offices?
a new WAN service supporting only IPv6
NAT overload to map inside IPv6 addresses to outside IPv4 address
a manually configured IPv6 tunnel between the edge routers R1 and R2
static NAT to map inside IPv6 addresses of the servers to an outside IPv4 ddress and dynamic NAT for the rest of the inside IPv6 addresses
5. Which variable is permitted or denied by a standard access control list?
protocol type
source IP address
source MAC address
destination IP address
destination MAC address
6. Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
The clock rate must be 56000.
The usernames are misconfigured.
The IP addresses are on different subnets.
The clock rate is configured on the wrong end of the link.
The CHAP passwords must be different on the two routers.
Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
7. Which three statements accurately describe a security policy? (Choose three.)
It creates a basis for legal action if necessary.
It defines a process for managing security violations.
It defines acceptable and unacceptable use of network resources.
The remote access policy is a component of the security policy that governs acceptable use of e-mail systems.
It is kept private from users to prevent the possibility of circumventing security measures.
It provides step-by-step procedures to harden routers and other network devices.
8. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
9.
Refer to the exhibit. Headquarters is connected through the Internet to branch office A and branch office B. Which WAN technology would be best suited to provide secure connectivity between headquarters and both branch offices?
ATM
VPN
ISDN
Frame Relay
broadband DSL
10. Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
11. A company is deciding which WAN connection type it should implement between its main office and branch offices. The company wants to use a cost-effective service that provides virtual circuits between each office. The company also wants to be able to transmit variable-length packets on these circuits. Which solution best meets these requirements?
ATM
HDLC
ISDN
Frame Relay
12. A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
Company 1 only uses microfilters at branch locations.
Company 1 has a lower volume of POTS traffic than company 2 has.
Company 2 is located farther from the service provider than company 1 is.
Company 2 shares the connection to the DSLAM with more clients than company 1 shares with.
13. Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the DC router to the Orlando router?
DLCI 123
DLCI 321
10.10.10.25
10.10.10.26
MAC address of the Orlando router
14. Refer to the exhibit. This router is being configured to use SDM, but the SDM interface of the router cannot be accessed. What is the cause of the problem?
The VTY lines are not configured correctly.
The HTTP timeout policy is not configured correctly.
The authentication method is not configured correctly.
The username and password are not configured correctly.
15. Which two devices can be used by teleworkers who need to connect to the company network across the PSTN for a few hours a day? (Choose two.)
router
CSU/DSU
DSL modem
cable modem
access server
dialup modem
16. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology.
Incorrect IPv4 addresses are entered on the router interfaces.
RIPng is incompatible with dual-stack technology.
IPv4 is incompatible with RIPng.
17. What is the function of an intrusion detection system on a network?
to restrict access to only authorized users
to detect attacks against a network and send logs to a management console
to prevents attack against the network and provide active defense mechanisms
to detect and prevent most viruses and many Trojan horse applications from spreading in the network
18. Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem?
The default gateway is in the wrong subnet.
STP has blocked the port that PC1 is connected to.
Port Fa0/2 on S2 is assigned to the wrong VLAN.
S2 has the wrong IP address assigned to the VLAN30 interface.
19. When Frame Relay encapsulation is used, what feature provides flow control and exchanges information about the status of virtual circuits?
LCP
LMI
DLCI
Inverse ARP
20. A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
Configure DHCP and static NAT.
Configure dynamic NAT for ten users.
Configure static NAT for all ten users.
Configure dynamic NAT with overload.
21. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
22. What will be the result of adding the command ip dhcp excluded-address 192.168.24.1 192.168.24.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 192.168.24.1 and 192.168.24.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 192.168.24.1 and 192.168.24.5.
The DHCP server will not issue the addresses ranging from 192.168.24.1 to 192.168.24.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 192.168.24.1 and 192.168.24.5.
23. Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from the DHCP server. The output of the debug ip dhcp server command shows “DHCPD: there is no address pool for 192.168.3.17″. What is the problem?
The address 192.168.3.17 address is already in use by Fa0/0.
The pool of addresses for the 192Network pool is configured incorrectly.
The ip helper-address command should be used on the Fa0/0 interface.
The 192.168.3.17 address has not been excluded from the 192Network pool.
24. Refer to the exhibit. From the output of the show interfaces and ping commands, at which layer of the OSI model is a fault indicated?
application
transport
network
data link
physical
25. What three questions can be answered using data gathered from a baseline on a new network? (Choose three.)
Are areas of the network experiencing high error rates?
Will the disaster recovery procedures work correctly?
What parts of the network have the highest volume?
Does the organization require more network technicians?
How does the network perform during peak periods?
Are there any devices working at top capacity?
What networks are the most susceptible to security attacks?
26. Which type of ACL will permit traffic inbound into a private network only if an outbound session has already been established between the source and destination?
extended
reflexive
standard
time-based
27. Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to Web Server. What is the destination IP address of the return packet from Web Server when received at R1?
10.1.1.2:80
10.1.1.2:1234
172.30.20.1:1234
172.30.20.1:3333
28. An administrator issues the command show interfaces s0/1/0 on a router that is configured for Frame Relay. Which console output may indicate an LMI mismatch?
Serial0/1/0 is administratively down
Serial0/1/0 is up, line protocol is up
Serial0/1/0 is up, line protocol is down
Serial0/1/0 is down, line protocol is down
29. A recently patched application server is experiencing response time problems. The network on which the application server is located has been experiencing occasional outages that the network team believes may be related to recent routing changes. Network and application teams have been notified to work on their respective issues. Which statement applies to this situation?
Only results from the software package should be tested as the network is designed to accommodate the proposed software platform.
Scheduling will be easy if the network and software teams work independently.
It will be difficult to isolate the problem if two teams are implementing changes independently.
Results from changes will be easier to reconcile and document if each team works in isolation.
30.
Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?
The PVC to R1 must be point-to-point.
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
31. Refer to the exhibit. Which VLAN will carry untagged traffic on FastEthernet 0/1?
VLAN 1
VLAN 2
VLAN 11
VLAN 12
VLAN 30
VLAN 999
32. What is an accurate description of CHAP when used with PPP on a serial connection between two routers?
A username and password are sent to the peer router, which replies with an accept or reject message.
A username and password are sent to the peer router. If these match the configuration in the peer, the peer in turn provides a username and password to the initiating router.
A challenge message is sent to the peer router, which responds with its username and a calculated value based on a shared secret. This value is then compared by the challenger to its own calculations.
An encrypted password is sent to the peer router, which decrypts it and compares it to a shared secret. If the decrypted passwords match, the peer sends the encrypted password back to the initiating router.
33. Where does a service provider assume responsibility from a customer for a WAN connection?
local loop
DTE cable on router
demarcation point
demilitarized zone
34. Refer to the exhibit. An ACL called Managers already exists on this router. What happens if the network administrator issues the commands as shown in the exhibit?
The commands are added to the end of the existing ACL.
The existing Managers ACL will be overwritten by the new ACL.
The router will output an error message and no changes will be made.
A duplicate Managers ACL will be created that will contain only the new commands.
35. Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
The password is unique and random.
PAP conducts periodic password challenges.
PAP uses MD5 hashing to keep the password secure.
36. Which combination of Layer 2 protocol and authentication should be used to establish a link without sending authentication information in plain text between a Cisco and a non-Cisco router?
PPP with PAP
PPP with CHAP
HDLC with PAP
HDLC with CHAP
37. Which option correctly defines the capacity through the local loop guaranteed to a customer by the service provider?
BE
DE
CIR
CBIR
38. Which wireless solution can provide mobile users with non line-of-sight broadband Internet access at speeds comparable to DSL or cable?
Wi-Fi
WiMAX
satellite
Metro Ethernet
39. Refer to the exhibit. EIGRP has been configured as a routing protocol on the network. Users on the 192.168.1.0/24 network should have full access to the web server that is connected to 192.168.3.0/24 but should not be allowed to telnet to router R3. Verifying the configuration, the network administrator realizes that users on network 192.168.1.0/24 can successfully telnet to the router. What should be done to remedy the problem?
The ACL 101 statements 10 and 20 should be reversed.
The ACL 101 should be applied on R3 VTY lines 0 4 in the inbound direction.
The ACL 101 should be applied on R3 VTY lines 0 4 in the outbound direction.
The ACL 101 should be applied on R3 Serial0/0/1 interface in the outbound direction.
The ACL 101 statement 10 should be changed to: permit ip 192.168.1.0 0.0.0.255 any
40. What does an access control list determine when used with NAT on a Cisco router?
addresses that are to be translated
addresses that are assigned to a NAT pool
addresses that are allowed out of the router
addresses that are accessible from the inside network
41. Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
172.16.0.0 0.0.0.1
172.16.0.0 0.0.0.3
172.16.0.0 0.0.0.7
172.16.0.0 255.255.255.252
42. Which security solution has the responsibility of monitoring suspicious processes that are running on a host and that might indicate infection of Trojan horse applications?
antivirus application
operating system patches
intrusion prevention system
Cisco Adaptive Security Appliance
43. Refer to the exhibit. A network administrator is trying to connect R1 remotely to make configuration changes. Based on the exhibited command output, what will be the result when attempting to connect to R1?
failure to connect due to Telnet not being enabled
failure to connect due to incomplete configuration for Telnet
a successful connection and ability to make configuration changes
a successful connection but inability to make configuration changes because of the absence of an enable secret password
44. Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
45. A technician has been asked to run the Cisco SDM one-step lockdown on a customer router. What will be the result of this process?
Traffic is only accepted from and forwarded to SDM-trusted Cisco routers.
Security testing is performed and the results are saved as a text file stored in NVRAM.
All traffic that enters the router is quarantined and checked for viruses before being forwarded.
The router is tested for any potential security problems and all recommended security-related configuration changes will be automatically applied.
46. Refer to the exhibit. Which data transmission technology is being represented?
TDM
PPP
HDLC
SLIP
47. A network administrator is instructing a technician on best practices for applying ACLs. Which two suggestions should the administrator provide? (Choose two.)
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied inside the core layer.
Place standard ACLs as close to the destination as possible.
ACLs applied to outbound interfaces require fewer router resources.
Extended ACLs should be applied closest to the source that is specified by the ACL.
48.Refer to the exhibit. Which configuration command would result in the output in the exhibit?
ip nat inside source static 10.1.200.254 172.16.76.3
ip nat inside source static 10.1.200.254 192.168.0.10
ip nat inside source static 172.16.76.3 10.1.200.254
ip nat inside source static 172.16.76.3 192.168.0.10
ip nat inside source static 192.168.0.10 172.16.76.3
ip nat inside source static 192.168.0.10 10.1.200.254
49. What are three important reasons to establish a network baseline? (Choose three.)
to determine the time it takes for the network to self recover from a failure
to determine which areas in the network are underutilized or overutilized
to determine the performance of the network during the normal hours of operation
to determine what thresholds should be set for the devices that need to be monitored
to determine the areas in the network which should not be included in the monitoring process
to determine the number of users whose access to network resources should be restricted
50. Which two statements are true about creating and applying access lists? (Choose two.)
There is an implicit deny at the end of all access lists.
One access list per port, per protocol, per direction is permitted.
Access list entries should filter in the order from general to specific.
The term “inbound” refers to traffic that enters the network from the router interface where the ACL is applied.
Standard ACLs should be applied closest to the source while extended ACLs should be applied closest to the destination.
51. While troubleshooting a problem with an e-mail server, an administrator observes that the switch port used by the server shows “up, line protocol up”. The administrator cannot ping the server. At which layer of the OSI model is the problem most likely to be found?
application layer
network layer
data link layer
physical layer
52. Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?
The ip rip authentication key-chain command specifies exam rather than test.
The name of the keystring is not the name of the neighboring router.
The key chains are given the same name on both routers.
The passive-interface command was issued for RTA.
1. Which functions are provided by LCP and NCP as part of the PPP layered architecture?
LCP sets up the PPP connection and its parameters. NCP terminates the PPP connection.
LCP sets up the PPP connection and its parameters. NCP handles higher layer protocol configurations.
LCP includes the link-establishment phase. NCP includes link-maintenance and link-termination phases.
LCP negotiates options for multiple network layer protocols. NCP agrees automatically on encapsulation formats.
2.Refer to the exhibit. EIGRP has been configured on routers R1 and R2. Connectivity across the Frame Relay switch between routers R1 and R2 is successfully verified using the ping command. However, no EIGRP routes are appearing in the routing table. What could be a cause for this failure?
The Frame Relay switch has failed.
The frame-relay map statement is incorrect.
The S0/0/0 interface of router R1 is administratively down.
The S0/0/0 interface of router R2 has an incorrect IP address.
3.Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
4.Refer to the exhibit. A network administrator is considering updating the IOS on Router1. What version of IOS is currently installed on Router1?
1
12.4
15
1841
5.Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the San Jose router to the DC router?
DLCI 103
DLCI 301
172.16.1.18
172.16.1.19
6. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
7.Refer to the exhibit. Partial results of the show access-lists and show ip interface FastEthernet 0/1 commands for router Router1 are shown. There are no other ACLs in effect. Host A is unable to telnet to host B. Which action will correct the problem but still restrict other traffic between the two networks?
Apply the ACL in the inbound direction.
Apply the ACL on the FastEthernet 0/0 interface.
Reverse the order of the TCP protocol statements in the ACL.
Modify the second entry in the list to permit tcp host 172.16.10.10 any eq telnet .
8. Which combination of authentication and Layer 2 protocol should be used to establish a link between a Cisco and a non-Cisco router without sending authentication information in plain text?
CHAP and HDLC
CHAP and PPP
PAP and HDLC
PAP and PPP
9. Which statement is true about wildcard masks?
A wildcard mask must be created by inverting the subnet mask.
A wildcard mask performs the same function as a subnet mask.
A wildcard mask of 0.0.0.0 means the address should match exactly.
A wildcard mask uses a "1" to identify IP address bits that must be checked.
10.Refer to the exhibit. ACL 120 is configured to allow traffic coming from 192.168.10.0/24 network to go to any destination limited to ports 80 and 443. ACL 130 should allow only requested HTTP traffic to flow back into the network. What additional configuration is needed in order for the access lists to fulfill the requirements?

11.Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
12.
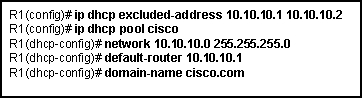
Refer to the exhibit. Which statement about the configuration is true?
10.10.10.1 is most likely assigned to the local LAN interface.
10.10.10.1 through 10.10.10.255 is available to be assigned to users.
All DHCP clients looking for an IP address will use 10.10.10.1 and 10.10.10.2.
All DHCP clients in the 10.10.10.0/24 network will use 10.10.10.2 as the default gateway.
13. Which statement is true about an interface that is configured with the IPv6 address command?
IPv6 traffic-forwarding is enabled on the interface.
A link-local IPv6 address is automatically configured on the interface.
A global unicast IPv6 address is dynamically configured the interface.
Any IPv4 addresses that are assigned to the interface are replaced with an IPv6 address.
14.Refer to the exhibit. Which data transmission technology is being represented?
TDM
PPP
HDLC
SLIP
15. Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
The password is unique and random.
PAP conducts periodic password challenges.
PAP uses MD5 hashing to keep the password secure.
16. What can a network administrator do to recover from a lost router password?
use the copy tftp: flash: command
boot the router to bootROM mode and enter the b command to load the IOS manually
telnet from another router and issue the show running-config command to view the password
boot the router to ROM monitor mode and configure the router to ignore the startup configuration when it initializes
17. A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
Configure static NAT.
Configure dynamic NAT.
Configure static NAT with overload.
Configure dynamic NAT with overload.
18. Which statement is true about the PPP authentication phase?
CHAP uses a 2-way handshake to exchange the credentials.
PAP can perform continuous authentication after a link is established.
CHAP sends an encrypted username and password during the authentication process.
The authentication phase takes place before the NCP configuration phase begins.
19.Refer to the exhibit. A network administrator is configuring Frame Relay on router HQ. It is desired that each Frame Relay PVC between the routers be in a separate subnet. Which two commands on HQ will accomplish this task for the connection to R1? (Choose two.)
HQ(config)# interface S0/0/0
HQ(config)# interface S0/0/0.1 multipoint
HQ(config)# interface S0/0/0.1 point-to-point
HQ(config-subif)# frame-relay interface dlci 103
HQ(config-subif)# frame-relay interface dlci 301
HQ(config-if)# frame-relay map ip 172.16.1.1 255.255.255.0 301 broadcast
20. Which wildcard mask would specify all IP addresses from 192.168.8.0 through 192.168.15.255?
0.0.0.7
0.0.7.255
0.0.8.255
0.0.15.255
0.0.255.255
21.Refer to the exhibit. WestSW is supposed to send VLAN information to EastSW, but that did not occur. What will force WestSW to send a VLAN update to EastSW?
Change EastSW to be a VTP server.
Reload both WestSW and EastSW at the same time.
Erase the VLAN database on EastSW and reload the switch.
Reset the configuration revision number on EastSW to zero.
Reload EastSW.
22. Which additional functionality is available on an interface when the encapsulation is changed from HDLC to PPP?
flow control
error control
authentication
synchronous communication
23. Which three guidelines would help contribute to creating a strong password policy? (Choose three.)
Once a good password is created, do not change it.
Deliberately misspell words when creating passwords.
Create passwords that are at least 8 characters in length.
Use combinations of upper case, lower case, and special characters.
Write passwords in locations that can be easily retrieved to avoid being locked out.
Use long words found in the dictionary to make passwords that are easy to remember.
24. Which three physical network problems should be checked when a bottom-up troubleshooting approach has been chosen to troubleshoot network performance? (Choose three.)
cable connectivity
high collision counts
STP failures and loops
address mapping errors
high CPU utilization rates
excess packets that are filtered by the firewall
25. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
26.Refer to the exhibit. Users who are connected to R1 report that they are unable to establish connectivity to the users who are connected to router R2. A network administrator tests the link with the debug ppp authentication command. Based on the output shown, which statement correctly defines the problem on the link?
R1 uses PAP as a method of authentication, and R2 uses CHAP.
R1 uses CHAP as a method of authentication, and R2 uses PAP.
R1 uses an incorrect user name or password for CHAP authentication.
R2 uses an incorrect user name or password for PAP authentication.
27.Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem?
The default gateway is in the wrong subnet.
STP has blocked the port that PC1 is connected to.
Port Fa0/2 on S2 is assigned to the wrong VLAN.
S2 has the wrong IP address assigned to the VLAN30 interface.
28. What is the result when the command permit tcp 192.168.4.0 0.0.3.255 any eq telnet is entered in an access control list and applied on the inbound interface of a router?
All traffic that originates from 192.168.4.0/24 is permitted.
All TCP traffic is permitted, and all other traffic is denied.
All Telnet traffic from the 192.168.0.0/16 network is permitted.
All traffic from the 192.168.4.0/22 network is permitted on TCP port 23.
29.Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?
The ip rip authentication key-chain command specifies exam rather than test.
The name of the keystring is not the name of the neighboring router.
The key chains are given the same name on both routers.
The passive-interface command was issued for RTA.
30. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology.
Incorrect IPv4 addresses are entered on the router interfaces.
RIPng is incompatible with dual-stack technology.
IPv4 is incompatible with RIPng.
31. Which encapsulation protocol when deployed on a Cisco router over a serial interface is only compatible with another Cisco router?
PPP
SLIP
HDLC
Frame Relay
32.Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses?
/19
/20
/21
/22
/23
/24
33. A technician has been asked to run Cisco SDM one-step lockdown on the router of a customer. What will be the result of this process?
Traffic is only forwarded from SDM-trusted Cisco routers.
Security testing is performed and the results are saved as a text file stored in NVRAM.
The router is tested for potential security problems and any necessary changes are made.
All traffic entering the router is quarantined and checked for viruses before being forwarded.
34. What translation method will allow a server to always keep the same public address?
static NAT
dynamic NAT
static NAT with overload
dynamic NAT with overload
35. A network administrator is tasked with maintaining two remote locations in the same city. Both locations use the same service provider and have the same service plan for DSL service. When comparing download rates, it is noticed that the location on the East side of town has a faster download rate than the location on the West side of town. How can this be explained?
The West side has a high volume of POTS traffic.
The West side of town is downloading larger packets.
The service provider is closer to the location on the East side.
More clients share a connection to the DSLAM on the West side.
36. A light manufacturing company wishes to replace its DSL service with a non-line-of-sight broadband wireless solution that offers comparable speeds. Which solution should the customer choose?
Wi-Fi
satellite
WiMAX
Metro Ethernet
37.Refer to the exhibit. Company ABC expanded its business and recently opened a new branch office in another country. IPv6 addresses have been used for the company network. The data servers Server1 and Server2 run applications which require end-to-end functionality, with unmodified packets that are forwarded from the source to the destination. The edge routers R1 and R2 support dual stack configuration. What solution should be deployed at the edge of the company network in order to successfully interconnect both offices?
a new WAN service supporting only IPv6
NAT overload to map inside IPv6 addresses to outside IPv4 address
a manually configured IPv6 tunnel between the edge routers R1 and R2
static NAT to map inside IPv6 addresses of the servers to an outside IPv4 address and dynamic NAT for the rest of the inside IPv6 addresses
38.Refer to the exhibit. Which statement correctly describes how Router1 processes an FTP request packet that enters interface S0/0/0, and is destined for an FTP server at IP address 172.16.1.5?
The router matches the incoming packet to the statement that is created by access-list 201 permit ip any any command and allows the packet into the router.
The router reaches the end of ACL 101 without matching a condition and drops the packet because there is no statement that was created by access-list 101 permit ip any any command.
The router matches the incoming packet to the statement that was created by the access-list 101 permit ip any 172.16.1.0 0.0.0.255 command, ignores the remaining statements in ACL 101, and allows the packet into the router.
The router matches the incoming packet to the statement that was created by the access-list 201 deny icmp 172.16.1.0 0.0.0.255 any command, continues comparing the packet to the remaining statements in ACL 201 to ensure that no subsequent statements allow FTP, and then the router drops the packet.
39. Which characteristic of VPN technology prevents the contents of data communications from being read by unauthorized parties?
QoS
latency
reliability
confidentiality
40. Which technology is used to dynamically map next hop, network layer addresses to virtual circuits in a Frame Relay network?
Inverse ARP
LMI
DLCI
FECN
41.Refer to the exhibit. A technician is teaching a trainee to interpret the results of various Frame Relay troubleshooting commands. What conclusion can be drawn from the output that is shown?
Neighboring routers should use DLCI 177 to reach the Branch router.
DLCI 177 will be used to identify all broadcasts that are sent out the Branch router.
The Branch router has the address 192.168.3.1 configured for the S0/0/0 interface.
To reach 192.168.3.1, the Branch router will use the virtual circuit that is identified by DLCI 177.
42. Where does a service provider assume responsibility from a customer for a WAN connection?
local loop
DTE cable on router
demarcation point
demilitarized zone
43. A company has its headquarters office in Dallas and five branch offices located in New York, Chicago, Los Angeles, Seattle, and Atlanta. WAN links are used for communications among offices in six sites. In planning the WAN links, the network designer is given two requirements: (1) minimize cost and (2) provide a certain level of WAN link reliability with redundant links. Which topology should the network designer recommend?
star
full mesh
hierarchical
partial mesh
44.Refer to the exhibit. A system administrator must provide connectivity to a foreign network for ten hosts in a small remote office. The commands that are listed in the exhibit were entered into the router that connects the foreign network. The users in the remote office report occasional failure to connect to resources in the foreign network. What is the likely problem?
The source addresses are not correctly designated.
The translated address pool is not correctly sized.
The access-list command is referencing the wrong addresses.
The wrong interface is designated as the source for translations.
45. An issue of response time has recently arisen on an application server. The new release of a software package has also been installed on the server. The configuration of the network has changed recently. To identify the problem, individuals from both teams responsible for the recent changes begin to investigate the source of the problem. Which statement applies to this situation?
Scheduling will be easy if the network and software teams work independently.
It will be difficult to isolate the problem if two teams are implementing changes independently.
Results from changes will be easier to reconcile and document if each team works in isolation.
Only results from the software package should be tested as the network is designed to accommodate the proposed software platform.
46. Which method is most effective in protecting the routing information that is propagated between routers on the network?
Disable IP source routing.
Configure passive interfaces.
Configure routing protocol authentication.
Secure administrative lines with Secure Shell.
47.
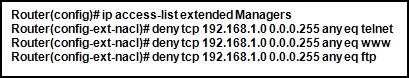
Refer to the exhibit. What happens if the network administrator issues the commands shown when an ACL called Managers already exists on the router?
The commands overwrite the existing Managers ACL.
The commands are added at the end of the existing Managers ACL.
The network administrator receives an error stating that the ACL already exists.
The commands will create a duplicate Managers ACL containing only the new commands being entered.
48. Which statement accurately describes a role that is played in establishing a WAN connection?
ISDN and ATM are circuit-switched technologies that are used to establish on demand a path through the service provider network.
Data link layer protocols like PPP and HDLC define how data is encapsulated for transmission across a WAN link.
A packet-switching network establishes a dedicated circuit between nodes for the duration of the communication session.
Frame Relay switches are normally considered to be customer premises equipment (CPE) and are maintained by local administrators.
49. What are two main components of data confidentiality? (Choose two.)
checksum
digital certificates
encapsulation
encryption
hashing
50. When NAT is in use, what is used to determine the addresses that can be translated on a Cisco router?
access control list
routing protocol
inbound interface
ARP cache
51.Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?
The PVC to R1 must be point-to-point.
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
52.Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 have not received any RIP routing updates. What will fix the issue?
Enable RIP authentication on R2.
Issue the ip directed-broadcast command on R2.
Change the subnet masks to 10.11.12.0/8 and 172.16.40.0/16 on R2.
Enable CDP on R2 so that the other routers will receive routing updates.
53. A network administrator can ping the Perth router, but gets a ‘Password Required but None Set’ message when trying to connect remotely via Telnet. Which command sequence must be applied to the Perth router to allow remote access?
Router(config)# line console 0 Router(config-line)# login Router(config-line)# password cisco
Router(config)# line vty 0 4 Router(config-line)# login Router(config-line)# password cisco
Router(config)# line virtual terminal Router(config-line)# enable login Router(config-line)# password cisco
Router(config)# line vty 0 4 Router(config-line)# enable secret Router(config-line)# password cisco
Router(config)# enable secret cisco Router(config)# enable cisco
54. A router does not load its configuration after a power failure. After running the show startup-configuration command, the administrator finds that the original configuration is intact. What is the cause of this problem?
The configuration register is set for 0×2100.
The configuration register is set for 0×2101.
The configuration register is set for 0×2102.
The configuration register is set for 0×2142. Boot system commands are not configured.
Flash memory is empty causing the router to bypass the configuration in NVRAM
checksum
digital certificates
encapsulation
encryption
hashing
2. Which network component has the primary function of detecting and logging attacks made against the network?
Cisco Security Agent
antivirus software scanner
intrusion detection system
intrusion prevention system
3.
Refer to the exhibit. A network administrator has issued the commands that are shown on Router1 and Router2. A later review of the routing tables reveals that neither router is learning the LAN network of the neighbor router. What is most likely the problem with the RIPng configuration?
The serial interfaces are in different subnets.
The RIPng process is not enabled on interfaces.
The RIPng network command is not configured.
The RIPng processes do not match between Router1 and Router2.
4. Which three guidelines would help contribute to creating a strong password policy? (Choose three.)
Once a good password is created, do not change it.
Deliberately misspell words when creating passwords.
Create passwords that are at least 8 characters in length.
Use combinations of upper case, lower case, and special characters.
Write passwords in locations that can be easily retrieved to avoid being locked out.
Use long words found in the dictionary to make passwords that are easy to remember.
5.
Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
The clock rate must be 56000.
The usernames are misconfigured.
The IP addresses are on different subnets.
The clock rate is configured on the wrong end of the link.
The CHAP passwords must be different on the two routers.
Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
6.
Refer to the exhibit. Headquarters is connected through the Internet to branch office A and branch office B. Which WAN technology would be best suited to provide secure connectivity between headquarters and both branch offices?
ATM
VPN
ISDN
Frame Relay
broadband DSL
7. Which combination of authentication and Layer 2 protocol should be used to establish a link between a Cisco and a non-Cisco router without sending authentication information in plain text?
CHAP and HDLC
CHAP and PPP
PAP and HDLC
PAP and PPP
8. A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
Company 2 downloads larger files than company 1 downloads.
Company 2 must share the connection to the DSLAM with more clients than company 1 shares.
Company 1 is closer to the service provider than is company 2.
Company 1 has a lower volume of POTS traffic than company 2 has.
9.
Refer to the exhibit. The network administrator creates a standard access control list to prohibit traffic from the 192.168.1.0/24 network from reaching the Internet. The access list must still permit the 192.168.1.0/24 network access to the 192.168.2.0 network. On which router interface and in which direction should the access control list be applied?
interface Fa0/0, inbound
interface Fa0/0, outbound
interface S0/0/0, inbound
interface S0/0/0, outbound
10. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology.
Incorrect IPv4 addresses are entered on the router interfaces.
RIPng is incompatible with dual-stack technology.
IPv4 is incompatible with RIPng.
11.
Refer to the exhibit. A network administrator is trying to backup the IOS software on R1 to the TFTP server. He receives the error message that is shown in the exhibit, and cannot ping the TFTP server from R1. What is an action that can help to isolate this problem?
Use correct source file name in the command.
Verify that the TFTP server software is running.
Make sure that there is enough room on the TFTP server for the backup.
Check that R1 has a route to the network where the TFTP server resides.
12.
Refer to the exhibit. Partial results of the show access-lists and show ip interface FastEthernet 0/1 commands for router Router1 are shown. There are no other ACLs in effect. Host A is unable to telnet to host B. Which action will correct the problem but still restrict other traffic between the two networks?
Apply the ACL in the inbound direction.
Apply the ACL on the FastEthernet 0/0 interface.
Reverse the order of the TCP protocol statements in the ACL.
Modify the second entry in the list to permit tcp host 172.16.10.10 any eq telnet .
13. What component of VPN technology combines message text with a key to make the message unreadable by unauthorized receivers?
message hash
user password
RSA signature
encryption algorithm
14. Which variable is permitted or denied by a standard access control list?
protocol type
source IP address
source MAC address
destination IP address
destination MAC address
15.
Refer to the exhibit. An ACL called Managers already exists on this router. What happens if the network administrator issues the commands as shown in the exhibit?
The new ACL overwrites the existing ACL.
The network administrator will receive an error message.
The existing ACL is modified to include the new command.
A second Managers ACL is created that contains only the new command.
16.
Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 have not received any RIP routing updates. What will fix the issue?
Enable RIP authentication on R2.
Issue the ip directed-broadcast command on R2.
Change the subnet masks to 10.11.12.0/8 and 172.16.40.0/16 on R2.
Enable CDP on R2 so that the other routers will receive routing updates.
17. What name is given to the location where a customer network interfaces with a network that is owned by another organization?
CPE
DCE
local loop
demarcation point
18.
Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the Orlando router to the DC router?
DLCI 123
DLCI 321
10.10.10.25
10.10.10.26
MAC address of the DC router
19.
Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
20. What will be the result of adding the command ip dhcp excluded-address 10.10.4.1 10.10.4.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 10.10.4.1 and 10.10.4.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 10.10.4.1 and 10.10.4.5.
The DHCP server will not issue the addresses ranging from 10.10.4.1 to 10.10.4.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 10.10.4.1 and 10.10.4.5.
21. What functionality do access control lists provide when implementing dynamic NAT on a Cisco router?
which addresses are allowed to be accessed from the inside network
which addresses are allowed out of the router
which addresses are assigned to a NAT pool
which addresses are to be translated
22. Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
23.
Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
24. An administrator is unable to receive e-mail. While troubleshooting the problem, the administrator is able to ping the local mail server IP address successfully from a remote network and can also successfully ping using the mail server name. At which layer of the OSI model is the problem most likely to be found?
physical layer
network layer
data link layer
application layer
25. Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
ATM
Frame Relay
HDLC
PPP
SDLC
26. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
27. Which statement accurately describes a role that is played in establishing a WAN connection?
ISDN and ATM are circuit-switched technologies that are used to establish on demand a path through the service provider network.
Data link layer protocols like PPP and HDLC define how data is encapsulated for transmission across a WAN link.
A packet-switching network establishes a dedicated circuit between nodes for the duration of the communication session.
Frame Relay switches are normally considered to be customer premises equipment (CPE) and are maintained by local administrators.
28.
Refer to the exhibit. What is the meaning of the term dynamic in the output of the command?
The bandwidth capability of the interface increases and decreases automatically based on BECNs.
The Serial0/0/1 interface acquired 172.16.3.1 from a DHCP server.
The mapping between DLCI 100 and 172.16.3.1 was learned through Inverse ARP.
DLCI 100 will automatically adapt to changes in the Frame Relay cloud.
29. What is an accurate description of CHAP when used with PPP on a serial connection between two routers?
A username and password are sent to the peer router, which replies with an accept or reject message.
A username and password are sent to the peer router. If these match the configuration in the peer, the peer in turn provides a username and password to the initiating router.
A challenge message is sent to the peer router, which responds with its username and a calculated value based on a shared secret. This value is then compared by the challenger to its own calculations.
An encrypted password is sent to the peer router, which decrypts it and compares it to a shared secret. If the decrypted passwords match, the peer sends the encrypted password back to the initiating router.
30. Which technology is used to dynamically map next hop, network layer addresses to virtual circuits in a Frame Relay network?
Inverse ARP
LMI
DLCI
31.
Refer to the exhibit. A network administrator is trying to connect R1 remotely to make configuration changes. Based on the exhibited command output, what will be the result when attempting to connect to R1?
failure to connect due to Telnet not being enabled
failure to connect due to incomplete configuration for Telnet
a successful connection and ability to make configuration changes
a successful connection but inability to make configuration changes because of the absence of an enable secret password
32. A DHCP server is configured with a block of excluded addresses. What two devices would be assigned static addresses from the excluded address range? (Choose two.)
a protocol analyzer
DNS server for the network
network printer that is used by many different users
a laptop that will get a different address each time it boots up
33.
Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses?
/19
/20
/21
/22
/23
/24
34. Compared with IDS systems, what can IPS systems do to provide further protection of computer systems?
detect potential attacks
stop the detected attack from executing
update OS patches for computer systems
scan computer systems for viruses and spyware
35. A company has its headquarters office in Dallas and five branch offices located in New York, Chicago, Los Angeles, Seattle, and Atlanta. WAN links are used for communications among offices in six sites. In planning the WAN links, the network designer is given two requirements: (1) minimize cost and (2) provide a certain level of WAN link reliability with redundant links. Which topology should the network designer recommend?
star
full mesh
hierarchical
partial mesh
36.
Refer to the exhibit. Every time the administrator reboots this router, the boot process ends in setup mode. What is a possible problem?
There is insufficient RAM for the IOS to load on this router.
A password recovery process should be done on this router.
The bootstrap version and the version of the IOS are different.
The IOS image is damaged and must be reloaded using tftpdnld.
The configuration register is set to ignore the startup configuration.
37. An administrator issues the command show interfaces s0/1/0 on a router that is configured for Frame Relay. Which console output may indicate an LMI mismatch?
Serial0/1/0 is administratively down
Serial0/1/0 is up, line protocol is up
Serial0/1/0 is up, line protocol is down
Serial0/1/0 is down, line protocol is down
38.Refer to the exhibit. Users who are connected to R1 report that they are unable to establish connectivity to the users who are connected to router R2. A network administrator tests the link with the debug ppp authentication command. Based on the output shown, which statement correctly defines the problem on the link?
R1 uses PAP as a method of authentication, and R2 uses CHAP.
R1 uses CHAP as a method of authentication, and R2 uses PAP.
R1 uses an incorrect user name or password for CHAP authentication.
R2 uses an incorrect user name or password for PAP authentication.
39. Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
172.16.0.0 0.0.0.1
172.16.0.0 0.0.0.3
172.16.0.0 0.0.0.7
172.16.0.0 255.255.255.252
40. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
41.
Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to the web server. What is the destination IP address of the return packet from the web server?
10.1.1.2:1234
172.30.20.1:1234
172.30.20.1:3333
192.168.1.2:80
42. What function does LCP perform in the establishment of a PPP session?
LCP brings the network layer protocols up and down.
It carries packets from several network layer protocols.
It encapsulates and negotiates options for IP and IPX.
It negotiates and sets up control options on the WAN data link.
43. An employee of XYZ corporation will begin working from home. The employee has a choice of DSL or cable technology for WAN connectivity. Which connectivity characteristic is accurately described?
Cable transfer rates are dependent on the length of the local loop.
DSL provides a high-speed connection over existing copper phone wires.
DSL download speeds are affected by high usage in the area.
DSL service shares the same frequency range as voice calls.
Cable connectivity usually requires new fiber installed for the local loop.
44. Which option represents a best practice for applying ACLs?
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied inside the core layer.
ACLs applied to outbound interfaces use fewer router resources.
Extended ACLs should be applied closest to the source that is specified by the ACL.
45. While troubleshooting a problem with an e-mail server, an administrator observes that the switch port used by the server shows “up, line protocol up”. The administrator cannot ping the server. At which layer of the OSI model is the problem most likely to be found?
application layer
network layer
data link layer
physical layer
46. Which two configurations must be completed before an RSA key can be generated on a router? (Choose two.)
a hostname
a domain name
the SSH version
the SSH timeouts
local authentication on the VTY lines
47. What type of ACL can be used to force a user to authenticate to the router before accessing a network?
standard
dynamic
reflexive
time-based
48. What is the result when the command security passwords min-length 8 is entered into a router?
All new passwords are required to be a minimum of 8 characters in length.
All current passwords are now required to be a minimum of 8 characters in length.
Enable passwords must be at least 8 characters but line passwords are unaffected.
Nothing will happen until the command service password-encryption is entered. Then all future passwords must have a minimum of 8 characters.
49. Because of a remote-procedure call failure, a user is unable to access an NFS server. At what layer of the TCP/IP model does this problem occur?
network layer
data link layer
physical layer
application layer
50. What is the result when the command permit tcp 10.25.132.0 0.0.0.255 any eq smtp is added to a named access control list and applied on the inbound interface of a router?
TCP traffic with a destination to the 10.25.132.0/24 is permitted.
Only Telnet traffic is permitted to the 10.24.132.0/24 network
Ttraffic from 10.25.132.0/24 is permitted to anywhere on using any port.
Traffic using port 25 from the 10.25.132.0/24 is permitted to all destinations.
—————
1.Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
2. Refer to the exhibit. A network administrator is tasked with completing the Frame Relay topology that interconnects two remote sites. How should the point-to-point subinterfaces be configured on HQ to complete the topology?
frame-relay interface-dlci 103 on Serial 0/0/0.1
frame-relay interface-dlci 203 on Serial 0/0/0.2
frame-relay interface-dlci 301 on Serial 0/0/0.1
frame-relay interface-dlci 302 on Serial 0/0/0.2
frame-relay map ip 192.168.1.1 103 broadcast on Serial 0/0/0.1
frame-relay map ip 192.168.2.2 203 broadcast on Serial 0/0/0.2
frame-relay map ip 192.168.1.1 301 broadcast on Serial 0/0/0.1
frame-relay map ip 192.168.2.2 302 broadcast on Serial 0/0/0.2
3. Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
ATM
Frame Relay
HDLC
PPP
SDLC
4. Refer to the exhibit. Company ABC expanded its business and recently opened a new branch office in another country. IPv6 addresses have been used for the company network. The data servers Server1 and Server2 run applications which require end-to-end functionality, with unmodified packets that are forwarded from the source to the destination. The edge routers R1 and R2 support dual stack configuration. What solution should be deployed at the edge of the company network in order to successfully interconnect both offices?
a new WAN service supporting only IPv6
NAT overload to map inside IPv6 addresses to outside IPv4 address
a manually configured IPv6 tunnel between the edge routers R1 and R2
static NAT to map inside IPv6 addresses of the servers to an outside IPv4 ddress and dynamic NAT for the rest of the inside IPv6 addresses
5. Which variable is permitted or denied by a standard access control list?
protocol type
source IP address
source MAC address
destination IP address
destination MAC address
6. Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
The clock rate must be 56000.
The usernames are misconfigured.
The IP addresses are on different subnets.
The clock rate is configured on the wrong end of the link.
The CHAP passwords must be different on the two routers.
Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
7. Which three statements accurately describe a security policy? (Choose three.)
It creates a basis for legal action if necessary.
It defines a process for managing security violations.
It defines acceptable and unacceptable use of network resources.
The remote access policy is a component of the security policy that governs acceptable use of e-mail systems.
It is kept private from users to prevent the possibility of circumventing security measures.
It provides step-by-step procedures to harden routers and other network devices.
8. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
9.
Refer to the exhibit. Headquarters is connected through the Internet to branch office A and branch office B. Which WAN technology would be best suited to provide secure connectivity between headquarters and both branch offices?
ATM
VPN
ISDN
Frame Relay
broadband DSL
10. Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
11. A company is deciding which WAN connection type it should implement between its main office and branch offices. The company wants to use a cost-effective service that provides virtual circuits between each office. The company also wants to be able to transmit variable-length packets on these circuits. Which solution best meets these requirements?
ATM
HDLC
ISDN
Frame Relay
12. A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
Company 1 only uses microfilters at branch locations.
Company 1 has a lower volume of POTS traffic than company 2 has.
Company 2 is located farther from the service provider than company 1 is.
Company 2 shares the connection to the DSLAM with more clients than company 1 shares with.
13. Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the DC router to the Orlando router?
DLCI 123
DLCI 321
10.10.10.25
10.10.10.26
MAC address of the Orlando router
14. Refer to the exhibit. This router is being configured to use SDM, but the SDM interface of the router cannot be accessed. What is the cause of the problem?
The VTY lines are not configured correctly.
The HTTP timeout policy is not configured correctly.
The authentication method is not configured correctly.
The username and password are not configured correctly.
15. Which two devices can be used by teleworkers who need to connect to the company network across the PSTN for a few hours a day? (Choose two.)
router
CSU/DSU
DSL modem
cable modem
access server
dialup modem
16. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology.
Incorrect IPv4 addresses are entered on the router interfaces.
RIPng is incompatible with dual-stack technology.
IPv4 is incompatible with RIPng.
17. What is the function of an intrusion detection system on a network?
to restrict access to only authorized users
to detect attacks against a network and send logs to a management console
to prevents attack against the network and provide active defense mechanisms
to detect and prevent most viruses and many Trojan horse applications from spreading in the network
18. Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem?
The default gateway is in the wrong subnet.
STP has blocked the port that PC1 is connected to.
Port Fa0/2 on S2 is assigned to the wrong VLAN.
S2 has the wrong IP address assigned to the VLAN30 interface.
19. When Frame Relay encapsulation is used, what feature provides flow control and exchanges information about the status of virtual circuits?
LCP
LMI
DLCI
Inverse ARP
20. A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
Configure DHCP and static NAT.
Configure dynamic NAT for ten users.
Configure static NAT for all ten users.
Configure dynamic NAT with overload.
21. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
22. What will be the result of adding the command ip dhcp excluded-address 192.168.24.1 192.168.24.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 192.168.24.1 and 192.168.24.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 192.168.24.1 and 192.168.24.5.
The DHCP server will not issue the addresses ranging from 192.168.24.1 to 192.168.24.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 192.168.24.1 and 192.168.24.5.
23. Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from the DHCP server. The output of the debug ip dhcp server command shows “DHCPD: there is no address pool for 192.168.3.17″. What is the problem?
The address 192.168.3.17 address is already in use by Fa0/0.
The pool of addresses for the 192Network pool is configured incorrectly.
The ip helper-address command should be used on the Fa0/0 interface.
The 192.168.3.17 address has not been excluded from the 192Network pool.
24. Refer to the exhibit. From the output of the show interfaces and ping commands, at which layer of the OSI model is a fault indicated?
application
transport
network
data link
physical
25. What three questions can be answered using data gathered from a baseline on a new network? (Choose three.)
Are areas of the network experiencing high error rates?
Will the disaster recovery procedures work correctly?
What parts of the network have the highest volume?
Does the organization require more network technicians?
How does the network perform during peak periods?
Are there any devices working at top capacity?
What networks are the most susceptible to security attacks?
26. Which type of ACL will permit traffic inbound into a private network only if an outbound session has already been established between the source and destination?
extended
reflexive
standard
time-based
27. Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to Web Server. What is the destination IP address of the return packet from Web Server when received at R1?
10.1.1.2:80
10.1.1.2:1234
172.30.20.1:1234
172.30.20.1:3333
28. An administrator issues the command show interfaces s0/1/0 on a router that is configured for Frame Relay. Which console output may indicate an LMI mismatch?
Serial0/1/0 is administratively down
Serial0/1/0 is up, line protocol is up
Serial0/1/0 is up, line protocol is down
Serial0/1/0 is down, line protocol is down
29. A recently patched application server is experiencing response time problems. The network on which the application server is located has been experiencing occasional outages that the network team believes may be related to recent routing changes. Network and application teams have been notified to work on their respective issues. Which statement applies to this situation?
Only results from the software package should be tested as the network is designed to accommodate the proposed software platform.
Scheduling will be easy if the network and software teams work independently.
It will be difficult to isolate the problem if two teams are implementing changes independently.
Results from changes will be easier to reconcile and document if each team works in isolation.
30.
Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?
The PVC to R1 must be point-to-point.
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
31. Refer to the exhibit. Which VLAN will carry untagged traffic on FastEthernet 0/1?
VLAN 1
VLAN 2
VLAN 11
VLAN 12
VLAN 30
VLAN 999
32. What is an accurate description of CHAP when used with PPP on a serial connection between two routers?
A username and password are sent to the peer router, which replies with an accept or reject message.
A username and password are sent to the peer router. If these match the configuration in the peer, the peer in turn provides a username and password to the initiating router.
A challenge message is sent to the peer router, which responds with its username and a calculated value based on a shared secret. This value is then compared by the challenger to its own calculations.
An encrypted password is sent to the peer router, which decrypts it and compares it to a shared secret. If the decrypted passwords match, the peer sends the encrypted password back to the initiating router.
33. Where does a service provider assume responsibility from a customer for a WAN connection?
local loop
DTE cable on router
demarcation point
demilitarized zone
34. Refer to the exhibit. An ACL called Managers already exists on this router. What happens if the network administrator issues the commands as shown in the exhibit?
The commands are added to the end of the existing ACL.
The existing Managers ACL will be overwritten by the new ACL.
The router will output an error message and no changes will be made.
A duplicate Managers ACL will be created that will contain only the new commands.
35. Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
The password is unique and random.
PAP conducts periodic password challenges.
PAP uses MD5 hashing to keep the password secure.
36. Which combination of Layer 2 protocol and authentication should be used to establish a link without sending authentication information in plain text between a Cisco and a non-Cisco router?
PPP with PAP
PPP with CHAP
HDLC with PAP
HDLC with CHAP
37. Which option correctly defines the capacity through the local loop guaranteed to a customer by the service provider?
BE
DE
CIR
CBIR
38. Which wireless solution can provide mobile users with non line-of-sight broadband Internet access at speeds comparable to DSL or cable?
Wi-Fi
WiMAX
satellite
Metro Ethernet
39. Refer to the exhibit. EIGRP has been configured as a routing protocol on the network. Users on the 192.168.1.0/24 network should have full access to the web server that is connected to 192.168.3.0/24 but should not be allowed to telnet to router R3. Verifying the configuration, the network administrator realizes that users on network 192.168.1.0/24 can successfully telnet to the router. What should be done to remedy the problem?
The ACL 101 statements 10 and 20 should be reversed.
The ACL 101 should be applied on R3 VTY lines 0 4 in the inbound direction.
The ACL 101 should be applied on R3 VTY lines 0 4 in the outbound direction.
The ACL 101 should be applied on R3 Serial0/0/1 interface in the outbound direction.
The ACL 101 statement 10 should be changed to: permit ip 192.168.1.0 0.0.0.255 any
40. What does an access control list determine when used with NAT on a Cisco router?
addresses that are to be translated
addresses that are assigned to a NAT pool
addresses that are allowed out of the router
addresses that are accessible from the inside network
41. Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
172.16.0.0 0.0.0.1
172.16.0.0 0.0.0.3
172.16.0.0 0.0.0.7
172.16.0.0 255.255.255.252
42. Which security solution has the responsibility of monitoring suspicious processes that are running on a host and that might indicate infection of Trojan horse applications?
antivirus application
operating system patches
intrusion prevention system
Cisco Adaptive Security Appliance
43. Refer to the exhibit. A network administrator is trying to connect R1 remotely to make configuration changes. Based on the exhibited command output, what will be the result when attempting to connect to R1?
failure to connect due to Telnet not being enabled
failure to connect due to incomplete configuration for Telnet
a successful connection and ability to make configuration changes
a successful connection but inability to make configuration changes because of the absence of an enable secret password
44. Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
45. A technician has been asked to run the Cisco SDM one-step lockdown on a customer router. What will be the result of this process?
Traffic is only accepted from and forwarded to SDM-trusted Cisco routers.
Security testing is performed and the results are saved as a text file stored in NVRAM.
All traffic that enters the router is quarantined and checked for viruses before being forwarded.
The router is tested for any potential security problems and all recommended security-related configuration changes will be automatically applied.
46. Refer to the exhibit. Which data transmission technology is being represented?
TDM
PPP
HDLC
SLIP
47. A network administrator is instructing a technician on best practices for applying ACLs. Which two suggestions should the administrator provide? (Choose two.)
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied inside the core layer.
Place standard ACLs as close to the destination as possible.
ACLs applied to outbound interfaces require fewer router resources.
Extended ACLs should be applied closest to the source that is specified by the ACL.
48.Refer to the exhibit. Which configuration command would result in the output in the exhibit?
ip nat inside source static 10.1.200.254 172.16.76.3
ip nat inside source static 10.1.200.254 192.168.0.10
ip nat inside source static 172.16.76.3 10.1.200.254
ip nat inside source static 172.16.76.3 192.168.0.10
ip nat inside source static 192.168.0.10 172.16.76.3
ip nat inside source static 192.168.0.10 10.1.200.254
49. What are three important reasons to establish a network baseline? (Choose three.)
to determine the time it takes for the network to self recover from a failure
to determine which areas in the network are underutilized or overutilized
to determine the performance of the network during the normal hours of operation
to determine what thresholds should be set for the devices that need to be monitored
to determine the areas in the network which should not be included in the monitoring process
to determine the number of users whose access to network resources should be restricted
50. Which two statements are true about creating and applying access lists? (Choose two.)
There is an implicit deny at the end of all access lists.
One access list per port, per protocol, per direction is permitted.
Access list entries should filter in the order from general to specific.
The term “inbound” refers to traffic that enters the network from the router interface where the ACL is applied.
Standard ACLs should be applied closest to the source while extended ACLs should be applied closest to the destination.
51. While troubleshooting a problem with an e-mail server, an administrator observes that the switch port used by the server shows “up, line protocol up”. The administrator cannot ping the server. At which layer of the OSI model is the problem most likely to be found?
application layer
network layer
data link layer
physical layer
52. Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?
The ip rip authentication key-chain command specifies exam rather than test.
The name of the keystring is not the name of the neighboring router.
The key chains are given the same name on both routers.
The passive-interface command was issued for RTA.
1. Which functions are provided by LCP and NCP as part of the PPP layered architecture?
LCP sets up the PPP connection and its parameters. NCP terminates the PPP connection.
LCP sets up the PPP connection and its parameters. NCP handles higher layer protocol configurations.
LCP includes the link-establishment phase. NCP includes link-maintenance and link-termination phases.
LCP negotiates options for multiple network layer protocols. NCP agrees automatically on encapsulation formats.
2.Refer to the exhibit. EIGRP has been configured on routers R1 and R2. Connectivity across the Frame Relay switch between routers R1 and R2 is successfully verified using the ping command. However, no EIGRP routes are appearing in the routing table. What could be a cause for this failure?
The Frame Relay switch has failed.
The frame-relay map statement is incorrect.
The S0/0/0 interface of router R1 is administratively down.
The S0/0/0 interface of router R2 has an incorrect IP address.
3.Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?
There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
4.Refer to the exhibit. A network administrator is considering updating the IOS on Router1. What version of IOS is currently installed on Router1?
1
12.4
15
1841
5.Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the San Jose router to the DC router?
DLCI 103
DLCI 301
172.16.1.18
172.16.1.19
6. A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
7.Refer to the exhibit. Partial results of the show access-lists and show ip interface FastEthernet 0/1 commands for router Router1 are shown. There are no other ACLs in effect. Host A is unable to telnet to host B. Which action will correct the problem but still restrict other traffic between the two networks?
Apply the ACL in the inbound direction.
Apply the ACL on the FastEthernet 0/0 interface.
Reverse the order of the TCP protocol statements in the ACL.
Modify the second entry in the list to permit tcp host 172.16.10.10 any eq telnet .
8. Which combination of authentication and Layer 2 protocol should be used to establish a link between a Cisco and a non-Cisco router without sending authentication information in plain text?
CHAP and HDLC
CHAP and PPP
PAP and HDLC
PAP and PPP
9. Which statement is true about wildcard masks?
A wildcard mask must be created by inverting the subnet mask.
A wildcard mask performs the same function as a subnet mask.
A wildcard mask of 0.0.0.0 means the address should match exactly.
A wildcard mask uses a "1" to identify IP address bits that must be checked.
10.Refer to the exhibit. ACL 120 is configured to allow traffic coming from 192.168.10.0/24 network to go to any destination limited to ports 80 and 443. ACL 130 should allow only requested HTTP traffic to flow back into the network. What additional configuration is needed in order for the access lists to fulfill the requirements?
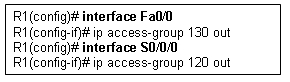

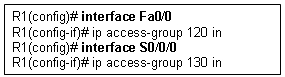
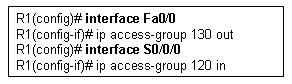
11.Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
12.
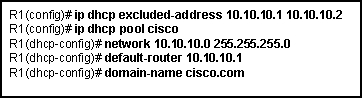
Refer to the exhibit. Which statement about the configuration is true?
10.10.10.1 is most likely assigned to the local LAN interface.
10.10.10.1 through 10.10.10.255 is available to be assigned to users.
All DHCP clients looking for an IP address will use 10.10.10.1 and 10.10.10.2.
All DHCP clients in the 10.10.10.0/24 network will use 10.10.10.2 as the default gateway.
13. Which statement is true about an interface that is configured with the IPv6 address command?
IPv6 traffic-forwarding is enabled on the interface.
A link-local IPv6 address is automatically configured on the interface.
A global unicast IPv6 address is dynamically configured the interface.
Any IPv4 addresses that are assigned to the interface are replaced with an IPv6 address.
14.Refer to the exhibit. Which data transmission technology is being represented?
TDM
PPP
HDLC
SLIP
15. Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
The password is unique and random.
PAP conducts periodic password challenges.
PAP uses MD5 hashing to keep the password secure.
16. What can a network administrator do to recover from a lost router password?
use the copy tftp: flash: command
boot the router to bootROM mode and enter the b command to load the IOS manually
telnet from another router and issue the show running-config command to view the password
boot the router to ROM monitor mode and configure the router to ignore the startup configuration when it initializes
17. A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
Configure static NAT.
Configure dynamic NAT.
Configure static NAT with overload.
Configure dynamic NAT with overload.
18. Which statement is true about the PPP authentication phase?
CHAP uses a 2-way handshake to exchange the credentials.
PAP can perform continuous authentication after a link is established.
CHAP sends an encrypted username and password during the authentication process.
The authentication phase takes place before the NCP configuration phase begins.
19.Refer to the exhibit. A network administrator is configuring Frame Relay on router HQ. It is desired that each Frame Relay PVC between the routers be in a separate subnet. Which two commands on HQ will accomplish this task for the connection to R1? (Choose two.)
HQ(config)# interface S0/0/0
HQ(config)# interface S0/0/0.1 multipoint
HQ(config)# interface S0/0/0.1 point-to-point
HQ(config-subif)# frame-relay interface dlci 103
HQ(config-subif)# frame-relay interface dlci 301
HQ(config-if)# frame-relay map ip 172.16.1.1 255.255.255.0 301 broadcast
20. Which wildcard mask would specify all IP addresses from 192.168.8.0 through 192.168.15.255?
0.0.0.7
0.0.7.255
0.0.8.255
0.0.15.255
0.0.255.255
21.Refer to the exhibit. WestSW is supposed to send VLAN information to EastSW, but that did not occur. What will force WestSW to send a VLAN update to EastSW?
Change EastSW to be a VTP server.
Reload both WestSW and EastSW at the same time.
Erase the VLAN database on EastSW and reload the switch.
Reset the configuration revision number on EastSW to zero.
Reload EastSW.
22. Which additional functionality is available on an interface when the encapsulation is changed from HDLC to PPP?
flow control
error control
authentication
synchronous communication
23. Which three guidelines would help contribute to creating a strong password policy? (Choose three.)
Once a good password is created, do not change it.
Deliberately misspell words when creating passwords.
Create passwords that are at least 8 characters in length.
Use combinations of upper case, lower case, and special characters.
Write passwords in locations that can be easily retrieved to avoid being locked out.
Use long words found in the dictionary to make passwords that are easy to remember.
24. Which three physical network problems should be checked when a bottom-up troubleshooting approach has been chosen to troubleshoot network performance? (Choose three.)
cable connectivity
high collision counts
STP failures and loops
address mapping errors
high CPU utilization rates
excess packets that are filtered by the firewall
25. A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
26.Refer to the exhibit. Users who are connected to R1 report that they are unable to establish connectivity to the users who are connected to router R2. A network administrator tests the link with the debug ppp authentication command. Based on the output shown, which statement correctly defines the problem on the link?
R1 uses PAP as a method of authentication, and R2 uses CHAP.
R1 uses CHAP as a method of authentication, and R2 uses PAP.
R1 uses an incorrect user name or password for CHAP authentication.
R2 uses an incorrect user name or password for PAP authentication.
27.Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem?
The default gateway is in the wrong subnet.
STP has blocked the port that PC1 is connected to.
Port Fa0/2 on S2 is assigned to the wrong VLAN.
S2 has the wrong IP address assigned to the VLAN30 interface.
28. What is the result when the command permit tcp 192.168.4.0 0.0.3.255 any eq telnet is entered in an access control list and applied on the inbound interface of a router?
All traffic that originates from 192.168.4.0/24 is permitted.
All TCP traffic is permitted, and all other traffic is denied.
All Telnet traffic from the 192.168.0.0/16 network is permitted.
All traffic from the 192.168.4.0/22 network is permitted on TCP port 23.
29.Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?
The ip rip authentication key-chain command specifies exam rather than test.
The name of the keystring is not the name of the neighboring router.
The key chains are given the same name on both routers.
The passive-interface command was issued for RTA.
30. An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology.
Incorrect IPv4 addresses are entered on the router interfaces.
RIPng is incompatible with dual-stack technology.
IPv4 is incompatible with RIPng.
31. Which encapsulation protocol when deployed on a Cisco router over a serial interface is only compatible with another Cisco router?
PPP
SLIP
HDLC
Frame Relay
32.Refer to the exhibit. The corporate network that is shown has been assigned network 172.16.128.0/19 for use at branch office LANs. If VLSM is used, what mask should be used for addressing hosts at Branch4 with minimal waste from unused addresses?
/19
/20
/21
/22
/23
/24
33. A technician has been asked to run Cisco SDM one-step lockdown on the router of a customer. What will be the result of this process?
Traffic is only forwarded from SDM-trusted Cisco routers.
Security testing is performed and the results are saved as a text file stored in NVRAM.
The router is tested for potential security problems and any necessary changes are made.
All traffic entering the router is quarantined and checked for viruses before being forwarded.
34. What translation method will allow a server to always keep the same public address?
static NAT
dynamic NAT
static NAT with overload
dynamic NAT with overload
35. A network administrator is tasked with maintaining two remote locations in the same city. Both locations use the same service provider and have the same service plan for DSL service. When comparing download rates, it is noticed that the location on the East side of town has a faster download rate than the location on the West side of town. How can this be explained?
The West side has a high volume of POTS traffic.
The West side of town is downloading larger packets.
The service provider is closer to the location on the East side.
More clients share a connection to the DSLAM on the West side.
36. A light manufacturing company wishes to replace its DSL service with a non-line-of-sight broadband wireless solution that offers comparable speeds. Which solution should the customer choose?
Wi-Fi
satellite
WiMAX
Metro Ethernet
37.Refer to the exhibit. Company ABC expanded its business and recently opened a new branch office in another country. IPv6 addresses have been used for the company network. The data servers Server1 and Server2 run applications which require end-to-end functionality, with unmodified packets that are forwarded from the source to the destination. The edge routers R1 and R2 support dual stack configuration. What solution should be deployed at the edge of the company network in order to successfully interconnect both offices?
a new WAN service supporting only IPv6
NAT overload to map inside IPv6 addresses to outside IPv4 address
a manually configured IPv6 tunnel between the edge routers R1 and R2
static NAT to map inside IPv6 addresses of the servers to an outside IPv4 address and dynamic NAT for the rest of the inside IPv6 addresses
38.Refer to the exhibit. Which statement correctly describes how Router1 processes an FTP request packet that enters interface S0/0/0, and is destined for an FTP server at IP address 172.16.1.5?
The router matches the incoming packet to the statement that is created by access-list 201 permit ip any any command and allows the packet into the router.
The router reaches the end of ACL 101 without matching a condition and drops the packet because there is no statement that was created by access-list 101 permit ip any any command.
The router matches the incoming packet to the statement that was created by the access-list 101 permit ip any 172.16.1.0 0.0.0.255 command, ignores the remaining statements in ACL 101, and allows the packet into the router.
The router matches the incoming packet to the statement that was created by the access-list 201 deny icmp 172.16.1.0 0.0.0.255 any command, continues comparing the packet to the remaining statements in ACL 201 to ensure that no subsequent statements allow FTP, and then the router drops the packet.
39. Which characteristic of VPN technology prevents the contents of data communications from being read by unauthorized parties?
QoS
latency
reliability
confidentiality
40. Which technology is used to dynamically map next hop, network layer addresses to virtual circuits in a Frame Relay network?
Inverse ARP
LMI
DLCI
FECN
41.Refer to the exhibit. A technician is teaching a trainee to interpret the results of various Frame Relay troubleshooting commands. What conclusion can be drawn from the output that is shown?
Neighboring routers should use DLCI 177 to reach the Branch router.
DLCI 177 will be used to identify all broadcasts that are sent out the Branch router.
The Branch router has the address 192.168.3.1 configured for the S0/0/0 interface.
To reach 192.168.3.1, the Branch router will use the virtual circuit that is identified by DLCI 177.
42. Where does a service provider assume responsibility from a customer for a WAN connection?
local loop
DTE cable on router
demarcation point
demilitarized zone
43. A company has its headquarters office in Dallas and five branch offices located in New York, Chicago, Los Angeles, Seattle, and Atlanta. WAN links are used for communications among offices in six sites. In planning the WAN links, the network designer is given two requirements: (1) minimize cost and (2) provide a certain level of WAN link reliability with redundant links. Which topology should the network designer recommend?
star
full mesh
hierarchical
partial mesh
44.Refer to the exhibit. A system administrator must provide connectivity to a foreign network for ten hosts in a small remote office. The commands that are listed in the exhibit were entered into the router that connects the foreign network. The users in the remote office report occasional failure to connect to resources in the foreign network. What is the likely problem?
The source addresses are not correctly designated.
The translated address pool is not correctly sized.
The access-list command is referencing the wrong addresses.
The wrong interface is designated as the source for translations.
45. An issue of response time has recently arisen on an application server. The new release of a software package has also been installed on the server. The configuration of the network has changed recently. To identify the problem, individuals from both teams responsible for the recent changes begin to investigate the source of the problem. Which statement applies to this situation?
Scheduling will be easy if the network and software teams work independently.
It will be difficult to isolate the problem if two teams are implementing changes independently.
Results from changes will be easier to reconcile and document if each team works in isolation.
Only results from the software package should be tested as the network is designed to accommodate the proposed software platform.
46. Which method is most effective in protecting the routing information that is propagated between routers on the network?
Disable IP source routing.
Configure passive interfaces.
Configure routing protocol authentication.
Secure administrative lines with Secure Shell.
47.
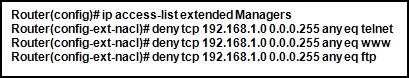
Refer to the exhibit. What happens if the network administrator issues the commands shown when an ACL called Managers already exists on the router?
The commands overwrite the existing Managers ACL.
The commands are added at the end of the existing Managers ACL.
The network administrator receives an error stating that the ACL already exists.
The commands will create a duplicate Managers ACL containing only the new commands being entered.
48. Which statement accurately describes a role that is played in establishing a WAN connection?
ISDN and ATM are circuit-switched technologies that are used to establish on demand a path through the service provider network.
Data link layer protocols like PPP and HDLC define how data is encapsulated for transmission across a WAN link.
A packet-switching network establishes a dedicated circuit between nodes for the duration of the communication session.
Frame Relay switches are normally considered to be customer premises equipment (CPE) and are maintained by local administrators.
49. What are two main components of data confidentiality? (Choose two.)
checksum
digital certificates
encapsulation
encryption
hashing
50. When NAT is in use, what is used to determine the addresses that can be translated on a Cisco router?
access control list
routing protocol
inbound interface
ARP cache
51.Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?
The PVC to R1 must be point-to-point.
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
52.Refer to the exhibit. RIPv2 has been configured on all routers in the network. Routers R1 and R3 have not received any RIP routing updates. What will fix the issue?
Enable RIP authentication on R2.
Issue the ip directed-broadcast command on R2.
Change the subnet masks to 10.11.12.0/8 and 172.16.40.0/16 on R2.
Enable CDP on R2 so that the other routers will receive routing updates.
53. A network administrator can ping the Perth router, but gets a ‘Password Required but None Set’ message when trying to connect remotely via Telnet. Which command sequence must be applied to the Perth router to allow remote access?
Router(config)# line console 0 Router(config-line)# login Router(config-line)# password cisco
Router(config)# line vty 0 4 Router(config-line)# login Router(config-line)# password cisco
Router(config)# line virtual terminal Router(config-line)# enable login Router(config-line)# password cisco
Router(config)# line vty 0 4 Router(config-line)# enable secret Router(config-line)# password cisco
Router(config)# enable secret cisco Router(config)# enable cisco
54. A router does not load its configuration after a power failure. After running the show startup-configuration command, the administrator finds that the original configuration is intact. What is the cause of this problem?
The configuration register is set for 0×2100.
The configuration register is set for 0×2101.
The configuration register is set for 0×2102.
The configuration register is set for 0×2142. Boot system commands are not configured.
Flash memory is empty causing the router to bypass the configuration in NVRAM
Set-3
1
Refer to the exhibit. Communication between two peers has failed. Based on the output that is shown, what is the most likely cause?
interface reset
unplugged cable
improper LMI type
PPP negotiation failure
2
Refer to the exhibit. A network administrator is tasked with completing the Frame Relay topology that interconnects two remote sites. How should the point-to-point subinterfaces be configured on HQ to complete the topology?

ccna 4 final 2012
frame-relay interface-dlci 103 on Serial 0/0/0.1
frame-relay interface-dlci 203 on Serial 0/0/0.2
frame-relay interface-dlci 203 on Serial 0/0/0.2
frame-relay interface-dlci 301 on Serial 0/0/0.1
frame-relay interface-dlci 302 on Serial 0/0/0.2
frame-relay interface-dlci 302 on Serial 0/0/0.2
frame-relay map ip 192.168.1.1 103 broadcast on Serial 0/0/0.1
frame-relay map ip 192.168.2.2 203 broadcast on Serial 0/0/0.2
frame-relay map ip 192.168.2.2 203 broadcast on Serial 0/0/0.2
frame-relay map ip 192.168.1.1 301 broadcast on Serial 0/0/0.1
frame-relay map ip 192.168.2.2 302 broadcast on Serial 0/0/0.2
frame-relay map ip 192.168.2.2 302 broadcast on Serial 0/0/0.2
3
Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
Which data link layer encapsulation protocol is used by default for serial connections between two Cisco routers?
ATM
Frame Relay
HDLC
PPP
SDLC
4
Refer to the exhibit. Company ABC expanded its business and recently opened a new branch office in another country. IPv6 addresses have been used for the company network. The data servers Server1 and Server2 run applications which require end-to-end functionality, with unmodified packets that are forwarded from the source to the destination. The edge routers R1 and R2 support dual stack configuration. What solution should be deployed at the edge of the company network in order to successfully interconnect both offices?
a new WAN service supporting only IPv6
NAT overload to map inside IPv6 addresses to outside IPv4 address
a manually configured IPv6 tunnel between the edge routers R1 and R2
static NAT to map inside IPv6 addresses of the servers to an outside IPv4 address and dynamic NAT for the rest of the inside IPv6 addresses
5
Which variable is permitted or denied by a standard access control list?
Which variable is permitted or denied by a standard access control list?
protocol type
source IP address
source MAC address
destination IP address
destination MAC address
6
Refer to the exhibit. The link between the CTRL and BR_1 routers is configured as shown in the exhibit. Why are the routers unable to establish a PPP session?
The clock rate must be 56000.
The usernames are misconfigured.
The IP addresses are on different subnets.
The clock rate is configured on the wrong end of the link.
The CHAP passwords must be different on the two routers.
Interface serial 0/0/0 on CTRL must connect to interface serial 0/0/1 on BR_1.
7
Which three statements accurately describe a security policy? (Choose three.)
Which three statements accurately describe a security policy? (Choose three.)
It creates a basis for legal action if necessary.
It defines a process for managing security violations.
It defines acceptable and unacceptable use of network resources.
The remote access policy is a component of the security policy that governs acceptable use of e-mail systems.
It is kept private from users to prevent the possibility of circumventing security measures.
It provides step-by-step procedures to harden routers and other network devices.
8
A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
A network administrator has changed the VLAN configurations on his network switches over the past weekend. How can the administrator determine if the additions and changes improved performance and availability on the company intranet?
Conduct a performance test and compare with the baseline that was established previously.
Interview departmental secretaries and determine if they think load time for web pages has improved.
Determine performance on the intranet by monitoring load times of company web pages from remote sites.
Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks.
9
Refer to the exhibit. Headquarters is connected through the Internet to branch office A and branch office B. Which WAN technology would be best suited to provide secure connectivity between headquarters and both branch offices?
ATM
VPN
ISDN
Frame Relay
broadband DSL
10
Which statement about a VPN is true?
Which statement about a VPN is true?
VPN link establishment and maintenance is provided by LCP.
DLCI addresses are used to identify each end of the VPN tunnel.
VPNs use virtual Layer 3 connections that are routed through the Internet.
Only IP packets can be encapsulated by a VPN for tunneling through the Internet.
11
A company is deciding which WAN connection type it should implement between its main office and branch offices. The company wants to use a cost-effective service that provides virtual circuits between each office. The company also wants to be able to transmit variable-length packets on these circuits. Which solution best meets these requirements?
A company is deciding which WAN connection type it should implement between its main office and branch offices. The company wants to use a cost-effective service that provides virtual circuits between each office. The company also wants to be able to transmit variable-length packets on these circuits. Which solution best meets these requirements?
ATM
HDLC
ISDN
Frame Relay
12
A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why company 1 reports higher download speeds than company 2 reports?
Company 1 only uses microfilters at branch locations.
Company 1 has a lower volume of POTS traffic than company 2 has.
Company 2 is located farther from the service provider than company 1 is.
Company 2 shares the connection to the DSLAM with more clients than company 1 shares with.
13
Refer to the exhibit. What is placed in the address field in the header of a frame that will travel from the DC router to the Orlando router?

DLCI 123
DLCI 321
10.10.10.25
10.10.10.26
MAC address of the Orlando router
14
Refer to the exhibit. This router is being configured to use SDM, but the SDM interface of the router cannot be accessed. What is the cause of the problem?

The VTY lines are not configured correctly.
The HTTP timeout policy is not configured correctly.
The authentication method is not configured correctly.
The username and password are not configured correctly.
15
Which two devices can be used by teleworkers who need to connect to the company network across the PSTN for a few hours a day? (Choose two.)
Which two devices can be used by teleworkers who need to connect to the company network across the PSTN for a few hours a day? (Choose two.)
router
CSU/DSU
DSL modem
cable modem
access server
dialup modem
16
An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
An administrator is configuring a dual stack router with IPv6 and IPv4 using RIPng. The administrator receives an error message when trying to enter the IPv4 routes into RIPng. What is the cause of the problem?
When IPv4 and IPv6 are configured on the same interface, all IPv4 addresses are over-written in favor of the newer technology.
Incorrect IPv4 addresses are entered on the router interfaces.
RIPng is incompatible with dual-stack technology.
IPv4 is incompatible with RIPng.
17
What is the function of an intrusion detection system on a network?
What is the function of an intrusion detection system on a network?
to restrict access to only authorized users
to detect attacks against a network and send logs to a management console
to prevents attack against the network and provide active defense mechanisms
to detect and prevent most viruses and many Trojan horse applications from spreading in the network
18
Refer to the exhibit. All devices are configured as shown in the exhibit. PC1 is unable to ping the default gateway. What is the cause of the problem?

The default gateway is in the wrong subnet.
STP has blocked the port that PC1 is connected to.
Port Fa0/2 on S2 is assigned to the wrong VLAN.
S2 has the wrong IP address assigned to the VLAN30 interface.
19
When Frame Relay encapsulation is used, what feature provides flow control and exchanges information about the status of virtual circuits?
When Frame Relay encapsulation is used, what feature provides flow control and exchanges information about the status of virtual circuits?
LCP
LMI
DLCI
Inverse ARP
20
A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
A system administrator must provide Internet connectivity for ten hosts in a small remote office. The ISP has assigned two public IP addresses to this remote office. How can the system administrator configure the router to provide Internet access to all ten users at the same time?
Configure DHCP and static NAT.
Configure dynamic NAT for ten users.
Configure static NAT for all ten users.
Configure dynamic NAT with overload.
21
A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
A company is looking for a WAN solution to connect its headquarters site to four remote sites. What are two advantages that dedicated leased lines provide compared to a shared Frame Relay solution? (Choose two.)
reduced jitter
reduced costs
reduced latency
the ability to burst above guaranteed bandwidth
the ability to borrow unused bandwidth from the leased lines of other customers
22
What will be the result of adding the command ip dhcp excluded-address 192.168.24.1 192.168.24.5 to the configuration of a local router that has been configured as a DHCP server?
What will be the result of adding the command ip dhcp excluded-address 192.168.24.1 192.168.24.5 to the configuration of a local router that has been configured as a DHCP server?
Traffic that is destined for 192.168.24.1 and 192.168.24.5 will be dropped by the router.
Traffic will not be routed from clients with addresses between 192.168.24.1 and 192.168.24.5.
The DHCP server will not issue the addresses ranging from 192.168.24.1 to 192.168.24.5.
The router will ignore all traffic that comes from the DHCP servers with addresses 192.168.24.1 and 192.168.24.5.
23
Refer to the exhibit. A host connected to Fa0/0 is unable to acquire an IP address from the DHCP server. The output of the debug ip dhcp server command shows “DHCPD: there is no address pool for 192.168.3.17″. What is the problem?
The address 192.168.3.17 address is already in use by Fa0/0.
The pool of addresses for the 192Network pool is configured incorrectly.
The ip helper-address command should be used on the Fa0/0 interface.
The 192.168.3.17 address has not been excluded from the 192Network pool.
24
Refer to the exhibit. From the output of the show interfaces and ping commands, at which layer of the OSI model is a fault indicated?

application
transport
network
data link
physical
25
What three questions can be answered using data gathered from a baseline on a new network? (Choose three.)
What three questions can be answered using data gathered from a baseline on a new network? (Choose three.)
Are areas of the network experiencing high error rates?
Will the disaster recovery procedures work correctly?
What parts of the network have the highest volume?
Does the organization require more network technicians?
How does the network perform during peak periods?
Are there any devices working at top capacity?
What networks are the most susceptible to security attacks?
26
Which type of ACL will permit traffic inbound into a private network only if an outbound session has already been established between the source and destination?
Which type of ACL will permit traffic inbound into a private network only if an outbound session has already been established between the source and destination?
extended
reflexive
standard
time-based
27
Refer to the exhibit. R1 is performing NAT overload for the 10.1.1.0/24 inside network. Host A has sent a packet to Web Server. What is the destination IP address of the return packet from Web Server when received at R1?

10.1.1.2:80
10.1.1.2:1234
172.30.20.1:1234
172.30.20.1:3333
28
An administrator issues the command show interfaces s0/1/0 on a router that is configured for Frame Relay. Which console output may indicate an LMI mismatch?
An administrator issues the command show interfaces s0/1/0 on a router that is configured for Frame Relay. Which console output may indicate an LMI mismatch?
Serial0/1/0 is administratively down
Serial0/1/0 is up, line protocol is up
Serial0/1/0 is up, line protocol is down
Serial0/1/0 is down, line protocol is down
29
A recently patched application server is experiencing response time problems. The network on which the application server is located has been experiencing occasional outages that the network team believes may be related to recent routing changes. Network and application teams have been notified to work on their respective issues. Which statement applies to this situation?
A recently patched application server is experiencing response time problems. The network on which the application server is located has been experiencing occasional outages that the network team believes may be related to recent routing changes. Network and application teams have been notified to work on their respective issues. Which statement applies to this situation?
Only results from the software package should be tested as the network is designed to accommodate the proposed software platform.
Scheduling will be easy if the network and software teams work independently.
It will be difficult to isolate the problem if two teams are implementing changes independently.
Results from changes will be easier to reconcile and document if each team works in isolation.
30
Refer to the exhibit. Branch A has a non-Cisco router that is using IETF encapsulation and Branch B has a Cisco router. After the commands that are shown are entered, R1 and R2 fail to establish the PVC. The R2 LMI is Cisco, and the R1 LMI is ANSI. The LMI is successfully established at both locations. Why is the PVC failing?

The PVC to R1 must be point-to-point.
LMI types must match on each end of a PVC.
The frame relay PVCs cannot be established between Cisco and non-Cisco routers.
The IETF parameter is missing from the frame-relay map ip 10.10.10.1 201 command.
31
Refer to the exhibit. Which VLAN will carry untagged traffic on FastEthernet 0/1?

VLAN 1
VLAN 2
VLAN 11
VLAN 12
VLAN 30
VLAN 999
32
What is an accurate description of CHAP when used with PPP on a serial connection between two routers?
What is an accurate description of CHAP when used with PPP on a serial connection between two routers?
A username and password are sent to the peer router, which replies with an accept or reject message.
A username and password are sent to the peer router. If these match the configuration in the peer, the peer in turn provides a username and password to the initiating router.
A challenge message is sent to the peer router, which responds with its username and a calculated value based on a shared secret. This value is then compared by the challenger to its own calculations.
An encrypted password is sent to the peer router, which decrypts it and compares it to a shared secret. If the decrypted passwords match, the peer sends the encrypted password back to the initiating router.
33
Where does a service provider assume responsibility from a customer for a WAN connection?
Where does a service provider assume responsibility from a customer for a WAN connection?
local loop
DTE cable on router
demarcation point
demilitarized zone
34
Refer to the exhibit. An ACL called Managers already exists on this router. What happens if the network administrator issues the commands as shown in the exhibit?

The commands are added to the end of the existing ACL.
The existing Managers ACL will be overwritten by the new ACL.
The router will output an error message and no changes will be made.
A duplicate Managers ACL will be created that will contain only the new commands.
35
Which statement is true about PAP in the authentication of a PPP session?
Which statement is true about PAP in the authentication of a PPP session?
PAP uses a two-way handshake.
The password is unique and random.
PAP conducts periodic password challenges.
PAP uses MD5 hashing to keep the password secure.
36
Which combination of Layer 2 protocol and authentication should be used to establish a link without sending authentication information in plain text between a Cisco and a non-Cisco router?
Which combination of Layer 2 protocol and authentication should be used to establish a link without sending authentication information in plain text between a Cisco and a non-Cisco router?
PPP with PAP
PPP with CHAP
HDLC with PAP
HDLC with CHAP
37
Which option correctly defines the capacity through the local loop guaranteed to a customer by the service provider?
Which option correctly defines the capacity through the local loop guaranteed to a customer by the service provider?
BE
DE
CIR
CBIR
38
Which wireless solution can provide mobile users with non line-of-sight broadband Internet access at speeds comparable to DSL or cable?
Which wireless solution can provide mobile users with non line-of-sight broadband Internet access at speeds comparable to DSL or cable?
Wi-Fi
WiMAX
satellite
Metro Ethernet
39
Refer to the exhibit. EIGRP has been configured as a routing protocol on the network. Users on the 192.168.1.0/24 network should have full access to the web server that is connected to 192.168.3.0/24 but should not be allowed to telnet to router R3. Verifying the configuration, the network administrator realizes that users on network 192.168.1.0/24 can successfully telnet to the router. What should be done to remedy the problem?

The ACL 101 statements 10 and 20 should be reversed.
The ACL 101 should be applied on R3 VTY lines 0 4 in the inbound direction.
The ACL 101 should be applied on R3 VTY lines 0 4 in the outbound direction.
The ACL 101 should be applied on R3 Serial0/0/1 interface in the outbound direction.
The ACL 101 statement 10 should be changed to: permit ip 192.168.1.0 0.0.0.255 any
40
What does an access control list determine when used with NAT on a Cisco router?
What does an access control list determine when used with NAT on a Cisco router?
addresses that are to be translated
addresses that are assigned to a NAT pool
addresses that are allowed out of the router
addresses that are accessible from the inside network
41
Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
Which IP address and wildcard mask combination can be used in an ACL statement to match the 172.16.0.0/30 network?
172.16.0.0 0.0.0.1
172.16.0.0 0.0.0.3
172.16.0.0 0.0.0.7
172.16.0.0 255.255.255.252
42
Which security solution has the responsibility of monitoring suspicious processes that are running on a host and that might indicate infection of Trojan horse applications?
Which security solution has the responsibility of monitoring suspicious processes that are running on a host and that might indicate infection of Trojan horse applications?
antivirus application
operating system patches
intrusion prevention system
Cisco Adaptive Security Appliance
43
Refer to the exhibit. A network administrator is trying to connect R1 remotely to make configuration changes. Based on the exhibited command output, what will be the result when attempting to connect to R1?

failure to connect due to Telnet not being enabled
failure to connect due to incomplete configuration for Telnet
a successful connection and ability to make configuration changes
a successful connection but inability to make configuration changes because of the absence of an enable secret password
44
Refer to the exhibit. Results of the show vlan and show vtp status commands for switches S1 and S2 are displayed in the exhibit. VLAN 11 was created on S1. Why is VLAN 11 missing from S2?

There is a Layer 2 loop.
The VTP domain names do not match.
Only one switch can be in server mode.
S2 has a higher spanning-tree priority for VLAN 11 than S1 does.
45
A technician has been asked to run the Cisco SDM one-step lockdown on a customer router. What will be the result of this process?
A technician has been asked to run the Cisco SDM one-step lockdown on a customer router. What will be the result of this process?
Traffic is only accepted from and forwarded to SDM-trusted Cisco routers.
Security testing is performed and the results are saved as a text file stored in NVRAM.
All traffic that enters the router is quarantined and checked for viruses before being forwarded.
The router is tested for any potential security problems and all recommended security-related configuration changes will be automatically applied.
46
Refer to the exhibit. Which data transmission technology is being represented?

TDM
PPP
HDLC
SLIP
47
A network administrator is instructing a technician on best practices for applying ACLs. Which two suggestions should the administrator provide? (Choose two.)
A network administrator is instructing a technician on best practices for applying ACLs. Which two suggestions should the administrator provide? (Choose two.)
Named ACLs are less efficient than numbered ACLs.
Standard ACLs should be applied inside the core layer.
Place standard ACLs as close to the destination as possible.
ACLs applied to outbound interfaces require fewer router resources.
Extended ACLs should be applied closest to the source that is specified by the ACL.
48
Refer to the exhibit. Which configuration command would result in the output in the exhibit?

ip nat inside source static 10.1.200.254 172.16.76.3
ip nat inside source static 10.1.200.254 192.168.0.10
ip nat inside source static 172.16.76.3 10.1.200.254
ip nat inside source static 172.16.76.3 192.168.0.10
ip nat inside source static 192.168.0.10 172.16.76.3
ip nat inside source static 192.168.0.10 10.1.200.254
49
What are three important reasons to establish a network baseline? (Choose three.)
What are three important reasons to establish a network baseline? (Choose three.)
to determine the time it takes for the network to self recover from a failure
to determine which areas in the network are underutilized or overutilized
to determine the performance of the network during the normal hours of operation
to determine what thresholds should be set for the devices that need to be monitored
to determine the areas in the network which should not be included in the monitoring process
to determine the number of users whose access to network resources should be restricted
50
Which two statements are true about creating and applying access lists? (Choose two.)
Which two statements are true about creating and applying access lists? (Choose two.)
There is an implicit deny at the end of all access lists.
One access list per port, per protocol, per direction is permitted.
Access list entries should filter in the order from general to specific.
The term “inbound” refers to traffic that enters the network from the router interface where the ACL is applied.
Standard ACLs should be applied closest to the source while extended ACLs should be applied closest to the destination.
51
While troubleshooting a problem with an e-mail server, an administrator observes that the switch port used by the server shows “up, line protocol up”. The administrator cannot ping the server. At which layer of the OSI model is the problem most likely to be found?
While troubleshooting a problem with an e-mail server, an administrator observes that the switch port used by the server shows “up, line protocol up”. The administrator cannot ping the server. At which layer of the OSI model is the problem most likely to be found?
application layer
network layer
data link layer
physical layer
52
Refer to the exhibit. Router RT is not receiving routing updates from router RTA. What is causing the problem?

The ip rip authentication key-chain command specifies exam rather than test.
The name of the keystring is not the name of the neighboring router.
The key chains are given the same name on both routers.
The passive-interface command was issued for RTA.




















Thanks for sharing some very good questions asked during the interviews. The most interesting thing that answers are also
ReplyDeletethere.
Regards
Silvester Norman
Change Mac Address
24
ReplyDeleteWhich two protocols in combination should be used to establish a link with secure authentication between a Cisco and a non-Cisco router? (Choose two.)
HDLC
*** PPP
SLIP
PAP
*** CHAP
****** http://tmy.se/3YC ******
ReplyDeletethe above link is very helpfull while studing ccna 200-120
it contain video class and pdf materials.
thanks for sharing excellent post & great blog
ReplyDeleteBy Sarah
Best CCNA Institute in Delhi
Can this be used on my CCNA 4 EWAN final test at thursday? or is there a newer version?
ReplyDelete#27 should be: "A congestion control mechanism is enabled on the Frame Relay connection."
ReplyDeleteThere are numerous errors in this posting. Corrections have been posted over at ccna4u.org.
ReplyDeleteThanQ for the answers it helped me clear the 4th final
ReplyDeleteI would like to share a list of Cisco exam-related articles and tips, at 100Questions Exam Portal (http://www.100qns.com) . CISCO 640-822 CCENT (100 Questions) is the Cisco Certified Networking Entry Technician exam, and covers the skills required for entry-level network support positions, and is the starting point for many networking careers. CCENT is the first step towards CCNA, and our exam volume prepares you to ace your exam.
ReplyDeleteCISCO CCNA Exam (100 Questions), or the Cisco Certified Network Associate validates the ability to install, configure, operate and troubleshoot medium-sized routed and switched networks. This includes basic mitigation of security threats, introduction to wireless networking concepts and terminology, and performance-based skills.
The other good thing is that you can test your Cisco knowledge and prepare for the exam via the exam library, which contains free-to-try exam questions. The Cisco reference section could be accessed from the drop-down menu, and because the portal covers several topics, it could be confusing initially due to the enormous amount of data, but if you spend some time navigating the contents you might be well-rewarded!
It was so nice article.I was really satisified by seeing this article and we are also giving CCNA CCNP online training.The ccna ccnp online training is one of the best ccna ccnp online training institute in worldwide.
ReplyDeleteGreat Blog ,TechnologyPartner.in Provide Free online CCNA Tutorial,CCNA Syllabus and online CCNA practice test , improve Networking skills To Students & CCNA Expert.
ReplyDeleteThanks for great post,Hub4Tech.com is provied CCNA Tutorial & CCNA Syllabus.CCNA Route & Switch Syllabus is Operation of IP Data Networks,LAN Switching Technologies,IP addressing (IPv4 /IPv6),IP Routing Technologies,IP Services,Network Device,Security,WAN Technologies.CCNA Online Test Paper.
ReplyDeleteGreat information about CCNP.. This is very helpful for us.
ReplyDeleteThank You!!
I would like to share one useful link for best study purpose on CCNP. You can get most useful CCNP Tutorial here.
Nice blog thanks for sharing info with us. Here we provide step by step solutions for those who wanna clear their certification in cca175 and cca500 for more info visit us @ cca175certification.com
ReplyDeletecca 500 certification
This information is very usefull.. thanks for sharing....
ReplyDeleteCCNA Training classes Kuwait
mcdonalds gutscheine | startlr | saludlimpia.net
ReplyDeleteThis is a good post. This post give truly quality information. I’m definitely going to look into it. Really very useful tips are provided here. thank you so much. Keep up the good works.
ReplyDeletepython course in pune
python course in chennai
python course in Bangalore
Great thoughts you got there, believe I may possibly try just some of it throughout my daily life.
ReplyDeleteJava interview questions and answers
Core Java interview questions and answers| Java interview questions and answers
Java training in Chennai | Java training in Tambaram
Java training in Chennai | Java training in Velachery
This blog is the general information for the feature. You got a good work for these blog.We have a developing our creative content of this mind.Thank you for this blog. This for very interesting and useful.
ReplyDeleteData Science course in Chennai | Best Data Science course in Chennai
Data science course in bangalore | Best Data Science course in Bangalore
Data science course in pune | Data Science Course institute in Pune
Data science online course | Online Data Science certification course-Gangboard
Data Science Interview questions and answers
Data Science Tutorial
Really good blog.
ReplyDeleteaws training in bangalore
Excellant post!!!. The strategy you have posted on this technology helped me to get into the next level and had lot of information in it.
ReplyDeleteAWS Training in pune
AWS Online Training
AWS Training in Bangalore
Superb.. Really it is an amazing article I had ever read. I hope it will help a lot for all. Thank you so much for this amazing post.
ReplyDeletemoto service center
motorola service center
motorola service center near me
ReplyDeleteNICE for giving a chance to share ideas for your comuty i really thanks for that great post.Best Ice Fishing Gloves Best Ice Fishing Gloves Best Ice Fishing Gloves
And indeed, I’m just always astounded concerning the remarkable things served by you. Some four facts on this page are undeniably the most effective I’ve had.
ReplyDeleteSLAJOBS REVIEWS AND COMPLAINTS
slajobs reviews and complaints
slajobs reviews and complaints
slajobs reviews and complaints
slajobs reviews and complaints
slajobs reviews and complaints
slajobs reviews and complaints
CFA program is aimed at enhancing the global financial management profession and investment management. The CFA program is designed to impart knowledge which is relevant to the professional career. CFA program emphasizes the highest ethical and professional standards. Whoever looking for a qualification to enhance their career in finance and establish financial credentials, CFA Exam is a good opportunity for them.
ReplyDeletehttps://www.edupristine.com/blog/about-cfa-exam
Hi thanks for tips on interview and skills i would like to share the list of boardingschoolinda
ReplyDeleteUttarakhand Govt jobs 2019, Uttarakhand Sarkari Naukri
ReplyDelete-------------------------------------------------------------------
http://uttrakhandcoldandcuttings.co.in/Uttarakhand-Govt-Jobs-2019.html
http://uttrakhandcoldandcuttings.co.in/Uttarakhand-Govt-Jobs-2019.html
DeleteBeing new to the blogging world I feel like there is still so much to learn. Your tips helped to clarify a few things for me as well as giving.devops Training in Bangalore
ReplyDeleteI gathered a lot of information through this article.Every example is easy to undestandable and explaining the logic easily.Amazon web services Training in Bangalore
ReplyDeleteReally thanks for sharing such an useful & informative stuff...
ReplyDeletedata analytics tutorial
Attend The Data Science Courses Bangalore From ExcelR. Practical Data Science Courses Bangalore Sessions With Assured Placement Support From Experienced Faculty. ExcelR Offers The Data Science Courses Bangalore.
ReplyDeleteExcelR Data Science Courses
Data Science Interview Questions
ExcelR Business Analytics Course
We are located at :
Location 1:
ExcelR - Data Science, Data Analytics Course Training in Bangalore
49, 1st Cross, 27th Main BTM Layout stage 1 Behind Tata Motors Bengaluru, Karnataka 560068
Phone: 096321 56744
Hours: Sunday - Saturday 7AM - 11PM
Location 2:
ExcelR
#49, Ground Floor, 27th Main, Near IQRA International School, opposite to WIF Hospital, 1st Stage, BTM Layout, Bengaluru, Karnataka 560068
Phone: 070224 51093
Hours: Sunday - Saturday 7AM - 10PM
Its really great being a content writer I can understand how tough is it to write and develop the content ,Thanks for sharing this wonderful informationSAP Training in Lucknow Digital marketing training in Lucknow AUTOCAD Training in Lucknow,
ReplyDeletePYthon Training in Lucknow, SAP FICO Training in Lucknow
Take admission in S.N Memorial Public School is Top CBSE School in Dehradun city, Bhauwala which offers English medium, secular, co-educational education from classes Nursery to XII.
ReplyDeleteThe School is affiliated to the Central Board of Secondary Education (CBSE).
CBSE school in Dehradun
Top School in Dehradun
Dehradun Famous School
Best school in Dehradun fees
Best Day Schools in Dehradun
Article is really Awesome.
ReplyDeleteData Science Training Course In Chennai | Data Science Training Course In Anna Nagar | Data Science Training Course In OMR | Data Science Training Course In Porur | Data Science Training Course In Tambaram | Data Science Training Course In Velachery
Dishis Designer Jewellery is Top Jewellery Store in Delhi. We are provide latest & unique design in Manga sutra, gemstone rings, nose pin, and earrings pendant. We are offers Free Shipping, Easy Return, Lifetime Exchange Policy. If you are more information than visit a website https://www.dishisjewels.com/
ReplyDeleteAfter reading your article I was amazed. I know that you explain it very well. And I hope that other readers will also experience how I feel after reading your article.
ReplyDeleteartificial intelligence course in bangalore
It is an informative blog. I would like to know more information about the new model bike. Anyway thanks a lot for sharing this post
ReplyDeleteData Science Training Course In Chennai | Certification | Online Course Training | Data Science Training Course In Bangalore | Certification | Online Course Training | Data Science Training Course In Hyderabad | Certification | Online Course Training | Data Science Training Course In Coimbatore | Certification | Online Course Training | Data Science Training Course In Online | Certification | Online Course Training
This is a wonderful article, Given so much info in it, These type of articles keeps the users interest in the website, and keep on sharing more ... good luck.
ReplyDeletemachine learning courses in bangalore
Thank you for sharing information. Wonderful blog & good post.
ReplyDeletebest pgdm courses in india
best pgdm institute in delhi
best pgdm institute in delhi ncr
best pgdm institute in india
I just stumbled upon your blog and wanted to say that I have really enjoyed reading your blog posts. Any way I’ll be subscribing to your feed and I hope you post again soon
ReplyDeleteNice information, valuable and excellent design, as share good stuff with good ideas and concepts, lots of great information and inspiration, both of which I need, thanks to offer such a helpful information
Java training in Chennai
Java Online training in Chennai
Java Course in Chennai
Best JAVA Training Institutes in Chennai
Java training in Bangalore
Java training in Hyderabad
Java Training in Coimbatore
Java Training
Java Online Training
nice post.Software Testing Training in Chennai | Certification | Online
ReplyDeleteCourses
Software Testing Training in Chennai
Software Testing Online Training in Chennai
Software Testing Courses in Chennai
Software Testing Training in Bangalore
Software Testing Training in Hyderabad
Software Testing Training in Coimbatore
Software Testing Training
Software Testing Online Training
Thanks for one marvelous posting! I enjoyed reading it; you are a great author. I will make sure to bookmark your blog and may come back someday. I want to encourage that you continue your great posts.
ReplyDeleteData Science Training In Chennai
Data Science Online Training In Chennai
Data Science Training In Bangalore
Data Science Training In Hyderabad
Data Science Training In Coimbatore
Data Science Training
Data Science Online Training
It is really a great and useful piece of info. I’m glad that you shared this helpful info with us. Please keep us informed like this. Thank you for sharing.
ReplyDeleteIELTS Coaching in chennai
German Classes in Chennai
GRE Coaching Classes in Chennai
TOEFL Coaching in Chennai
spoken english classes in chennai | Communication training
It is really great post thanks for sharing.
ReplyDeleteacte reviews
acte velachery reviews
acte tambaram reviews
acte anna nagar reviews
acte porur reviews
acte omr reviews
acte chennai reviews
acte student reviews
this is really too useful and have more ideas from yours. keep sharing many techniques. eagerly waiting for your new blog and useful information. keep doing more.
ReplyDeleteAWS Course in Chennai
AWS Course in Bangalore
AWS Course in Hyderabad
AWS Course in Coimbatore
AWS Course
AWS Certification Course
AWS Certification Training
AWS Online Training
AWS Training
Useful content, I have bookmarked this page for my future reference.
ReplyDelete| Certification | Cyber Security Online Training Course | Ethical Hacking Training Course in Chennai | Certification | Ethical Hacking Online Training Course | CCNA Training Course in Chennai | Certification | CCNA Online Training Course | RPA Robotic Process Automation Training Course in Chennai | Certification | RPA Training Course Chennai | SEO Training in Chennai | Certification | SEO Online Training Course
Good Post! , it was so good to read and useful to improve my knowledge as an updated one, keep blogging.After seeing your article I want to say that also a well-written article with some very good information which is very useful for the readers....thanks for sharing it and do share more posts likethis
ReplyDeletehttps://www.3ritechnologies.com/course/online-python-certification-course/
Detectives privados Madrid Asociados es un despacho de investigación privada en Madrid con gran experiencia. Contacta con los mejores detectives privados en Madrid para todo tipo de investigaciones privadas.
ReplyDeletedetectives privados madrid
agencia detectives Madrid
Thank you..
This blog is really helpful to deliver updated educational affairs over internet which is really appraisable. I found one successful example of this truth through this blog. I am going to use such information now
ReplyDeleteData Science Training in Chennai
Data Science Training in Velachery
Data Science Training in Tambaram
Data Science Training in Porur
Data Science Training in Omr
Data Science Training in Annanagar
Nice blog.Check this Ethical Hacking Training In Bangalore
ReplyDeleteNice blog. Check this Best Ethical Hacking Training In Bangalore
ReplyDeleteПервоначальные приемы хиромантии родились за несколько тысяч лет до нашей эры. Синоптичные катаклизмы или обрядовые приношения животных в дар со временем обосновали точное разъснение увиденного. Гадание на любимого считается максимально достоверным вариантом просмотреть грядущее личности.
ReplyDeleteОтделывают стены и полы керамикой в целом вследствие её физических особенностей. Каждый посетитель, приобретая керамику на сайте ibero b, получает на самом деле отличный продукт. Для того чтобы купить плитку в магазине sotni.ru, необходимо просто открыть официальный сайт фирмы. Прямая и гладкая плоскость очень просто моется.
ReplyDeleteКомпания «Скоро Деньги» предоставляет всем потребителям вивус онлайн и шанс выбора коммерческих организаций. Клиентам на этот раз не потребуется посещать кредитную организацию, с целью оформить требуемую сумму. Лично выбирайте подходящий финансовый продукт для различных нужд.
ReplyDeleteГадание на таро познай себе это вариант рассмотреть грядущие события всегда завлекал род людской. Гадание дозволяет предположить, что вас ожидает в предстоящее время. Любой жаждет предугадать собственную судьбу и считает конкретные типы ворожбы максимально действенными.
ReplyDeleteBest IT Training in Chennai
ReplyDeleteBest lms software
ReplyDeleteBest virtual classroom
zoom alternative
best learning management system
online learning management system software
Онлайн-автоматы во все времена манили игроков. Casino x официальный сайт зеркало – используйте все преимущества надежной игральной площадки, зарабатывайте серьезные суммы. Отныне любой желающий может опробовать судьбу на странице Casino X.
ReplyDeleteПолучайте настоящее наслаждение, играясь в подходящей компании сторонников. На представленной странице играть в мистер бит онлайн на деньги представлено масса важной информации о компьютерных играх. По игрушкам определенного назначения проводят международные соревнования. Обилие сетевых игр растет с каждым годом.
ReplyDeleteВ настоящее время существуют тысячи веб-казино на реальные денежки. Лишь на сайте как зарегистрироваться в джойказино клеенты смогут выиграть серьезные деньги. Стоит уделить особое внимание подбору наиболее надежного игрального сайта.
ReplyDeleteI've been looking for info on this topic for a while. I'm happy this one is so great. Keep up the excellent work ExcelR Data Analytics Courses
ReplyDeleteПрикрашивают стенки и пол керамикой прежде всего из-за её практических особенностей. Прямая и гладкая плоскость довольно просто протирается. Любой пользователь, приобретая керамику в онлайн-магазине coliseumgres лугано, получает действительно отличный товар. Для того чтобы купить плитку в магазине sotni.ru, необходимо просто посетить официальный сайт производителя.
ReplyDeleteExcelR provides Data Analytics courses. It is a great platform for those who want to learn and become a Data Analytics course. Students are tutored by professionals who have a degree in a particular topic. It is a great opportunity to learn and grow.
ReplyDeleteData Analytics courses
Nice Article
ReplyDeletehttps://java-latte.blogspot.com/2014/03/metaspace-in-java-8.html?showComment=1616145785427#c6857116651072357475
Nice Article
ReplyDeleteClinical Research Courses
По-своему выбирайте направление путешествия и время отправления Ж/Д состава. Сегодня всякий человек сможет своими силами продумать своё путешествие без дополнительных переплат. Именно на информационном сайте https://biletynapoezda.ru/novosibirsk-yurga/ вы можете заказывать билеты онлайн.
ReplyDeleteКстати, вам может пригодиться турки купить спб, все разнится от определенного места отдыха. Популярные игры и атрибуты для подвижных игр также необходимы на открытом воздухе. Приобрести желаемый спортинвентарь отдыхая на природе вы сможете благодаря огромному каталогу снаряжения для спортивного отдыха сайта МегаМаг.
ReplyDeleteАбитуриенту понадобится в пределах $15 000 - $20 000 ежегодно на образование, сумма будет измениться от университета, где осуществляется образование. Институты США не выделяют бесплатные места иностранцам. Абитуриенты из других государств получат подготовку в Америке непосредственно заплатив за все обучение. Непосредственно за счет https://liport.ru/obschestvo/440539-obrazovanie-v-ssha-pomosch-v-postuplenii-ot-kompanii-infostudy.html вы сможете получить престижное образование и начать стремительную карьеру. Особо подкованные иностранцы могут надеяться на небольшую льготу в обучении.
ReplyDeleteGood blog,
ReplyDeleteACCA Coaching kerala, ACCA Coaching Center in kerala, ACCA Classes in kerala, ACCA Coaching Classes kerala, Best ACCA Coaching in kerala, No:1 ACCA Coaching Center in kerala, Top 10 ACCA Coaching Centers in kerala, ACCA Online Courses, ACCA Training, ACCA IFRS course, ACCA IFRS Certification, ACCA Online Coaching, ACCA Certification Courses, ACCA SBR Online Courses
https://ffacademia.com
Множество молодых людей думают получить качественную подготовку в зарубежных странах. На странице фирмы https://newspotok.ru/2021/04/23/chastnye-shkoly-v-kanade.html в наличии огромнейший каталог учебных образований, в каких сможет устроиться какой угодно человек. Info Study помогает поступить в колледжи Канады.
ReplyDeleteБинты для спорта на совесть защитятсохранят твои руки от травмирований в период занятий. Выступая на различных турнирах тебе в обязательном порядке нужны купить настенную сушилку для белья на балкон, найти какие очень просто в онлайн-магазине Яндекс. Спорт – это простой вариант поправить здоровье.
ReplyDeleteДля внутрикомнатных работ применять смоляно фенолформальдегидную фанеру невозможно - могут выделяться вредные субстанции при определенных ситуациях. По большей части ФСФ фанеру используют как наружный облицовочный материал. Не пропускающий воду тип фактически не втягивает влагу, а уже после высыхания возвращается к своей первоначальной форме. Фанерная плита ФСФ - это влагостойкий подтип фанеры, получивший разнообразное расширение в строительной сфере https://xn--80aao5aqu.xn--90ais/.
ReplyDeleteinteresting to read
ReplyDeleteAngular training in Chennai
Объем потока воздуха сушилки считается основным критериумом для подборки сушилки. Чем плотнее воздушный поток, тем оперативнее пользователь решит свои дела в туалете. Подбирайте https://smartdryer.ru/category/sushilki-dlya-ruk/vysokoskorostnye-jet/ современные установки на платформе smartdryer.ru для улучшения качества обслуживания пользователей. По большей части воздушный поток проходит по рукам непосредственно вертикально, но находятся и «погружные» варианты, на манер аккуратного ящичка, куда придется располагать руки сверху вниз.
ReplyDeleteGreat information!!! Thanks for your wonderful informative blog.
ReplyDeleteVillage Talkies a top-quality professional corporate video production company in Bangalore and also best explainer video company in Bangalore & animation video makers in Bangalore, Chennai, India & Maryland, Baltimore, USA provides Corporate & Brand films, Promotional, Marketing videos & Training videos, Product demo videos, Employee videos, Product video explainers, eLearning videos, 2d Animation, 3d Animation, Motion Graphics, Whiteboard Explainer videos Client Testimonial Videos, Video Presentation and more for all start-ups, industries, and corporate companies. From scripting to corporate video production services, explainer & 3d, 2d animation video production , our solutions are customized to your budget, timeline, and to meet the company goals and objectives.
As a best video production company in Bangalore, we produce quality and creative videos to our clients.
This is my first time visiting here and I found so much interesting stuff in your blog, especially it's discussion, thank you.
ReplyDeletedata scientist training and placement in hyderabad
Davao Medical School foundation
ReplyDeleteDMSF
colleges in the Philippines
Transworld Educare
DMSF
KIMA
Kings International Medical Academy
Благодаря копирайтингу элементарно получать отличную прибыть. На площадке сайт тор зайти на гидру наверняка представлена работа даже для юных фрилансеров. Проекты для фрилансеров – это самый элементарный любому исполнителю метод заработка в интернете. На подобных сайтах заказчики выкладывают особенные цели, сделав какие работник получит баллы на личный ID аккаунта.
ReplyDeleteбольшинство получают проблему анонимного перевода электронных платежей. Работа на удаленке, возьмем например, фрилансер, различные работодателиЕсть значительное число проектов, которые дают шанс перечислить денежные средства совершенно без возможности отследить ссылка на сайт. Принять скрытый платеж в интернет сети не так уж и просто, вместе с тем, по факту реально.
ReplyDeleteClinical Research Courses
ReplyDeleteОнлайн магазин Hydra – это оперативные закупки и оптимальные цены. По большей части, покупки при наличии гаранта осуществляются мгновенно, вам остается лишь зайти на место раздачи и принять свои заказы. Внутренний ИИ не будет требовать посетителя заполнить собственные сведения. Покупки по особенно доступной цене на https://hydra.tor.com/ – это существенная экономия денежных средств. Заказать желаемые товары по максимально подходящей цене юзер сумеет лишь на перспективной платформе ГидраРУ.
ReplyDeleteReally nice and interesting post. I was looking for this kind of information and enjoyed reading this one. Keep posting. Thanks for sharing.
ReplyDeletedata science course
AI Patasala is the most rumoured Python Training in Hyderabad developed to help you advance your career with a massive increase in the latest technology.
ReplyDeletePython Course Hyderabad
Блокчейн переводы плотно пускают корни в нашу жизнь. Криптовалюты – является актуальным вариантом виртуальных денежных средств. Приобретая крипто валюту, реально отлично заработать, подождав ее изменения в стоимости. На сайте https://s-usd.com/ кто угодно может просчитать важность скупки той или иной виртуальной валюты.
ReplyDeleteПокрытые краской диски http://fddytht.vidown.cn/bbs/home.php?mod=space&uid=393986 не только улучшают внешность дисков, но и помогают их охране от разрушительнейшего воздействия. Разрушающее воздействие агрессивной атмосферы критически ощущается на внешнем состоянии колес каждой машины. В случае если окрасить колеса самолично, спустя время напыление станет шелушиться, вновь раскрывая поверхностный слой.
ReplyDeleteГидраРУ значится особенно большим сайтом, который предоставляет вещи своеобразного потребления. Крутой магазин http://fddhtvq.vidown.cn/bbs/home.php?mod=space&uid=393162 размещен в невидимой части мировой сети. Великое множество поставщиков и актуальная стоимость – вот главные положительные обстоятельства, за счет чего покупатели скупляются в Гидра РУ.
ReplyDeleteСайт мониторинга обменников оФФ дает своим пользователям десятки лицензированных компаний. Пункты обмена виртуальных валют в любом случае оформили лицензию. Любые валютные обмены на страницах оФФ прошли характерную проверку. Воспользуйтесь сайтом http://www.mzdbdx.cn/home.php?mod=space&uid=216476 и осознайте основные преимущества благоприятной обменной операции.
ReplyDeleteХидра – это инновационный магазин, на котором есть возможность закупить требуемые продукты по оптимально хорошей цене. Виртуальный магазин занимается продажами на протяжении шести лет, и за такой отрезок времени умудрился зарекомендовать себя как выдающаяся торговая площадка. В настоящий момент 90% определенных торговых сделок осуществляют в интернете. На форуме http://xn-----mlcac6bdefdqdsdch1bs.xn--p1ai/index.php?subaction=userinfo&user=ekuqysiw вы имеете возможность обнаружить продукты на свой вкус и стоимость.
ReplyDeleteПо требованию покупателя допускается незначительно откорректировать формат проектного парогенератора, применительно технологических требований. При подборе агрегата https://wowx.org/member.php?99514-ovewexu покупателям будет оказана консультация инженеров завода «РЭП» Барнаула. Высококвалифицированные специалисты фирмы оперативно помогут найти конкретные агрегаты по выработке пара.
ReplyDeleteЗабронировать билеты сегодня возможно через интернет https://krasnodar-avtovokzal.ru/maykop-krasnodar/, не покидая своего жилья или офиса. Дни, когда за талонами на автобус была необходимость отстаивать часами в ожидании в окошке автовокзала, уже забыты. Когда вы направляетесь в другой город, лучше тут же взять билет на обратный путь, это позволяет вам незначительно экономить.
ReplyDeleteUPVC Pipe Market Size, Analytical Overview, Outlook, Growth Situation Future And Demand 2022- 2028
ReplyDeleteSummary
A New Market Study, Titled “UPVC Pipe Market Upcoming Trends, Growth Drivers and Challenges” has been featured on fusionmarketresearch.
This report provides in-depth study of ‘UPVC Pipe Market ‘using SWOT analysis i.e. strength, weakness, opportunity and threat to Organization. The UPVC Pipe Market report also provides an in-depth survey of major market players which is based on the various objectives of an organization such as profiling, product outline, production quantity, raw material required, and production. The financial health of the organization.
UPVC Pipe Market
Radiation Protection Curtain Market Status (2016-2020) and Forecast (2021E-2028F) by Region, Product Type & End-Use
ReplyDeleteRadiation Protection Curtain market
Overview
At the beginning of a recently published report on the global Radiation Protection Curtain market, extensive analysis of the industry has been done with an insightful explanation. The overview has explained the potential of the market and the role of key players that have been portrayed in the information that revealed the applications and manufacturing technology required for the growth of the global Radiation Protection Curtain market.
Radiation Protection Curtain market
Red Rice Red Market Status (2016-2020) and Forecast (2021E-2028F) by Region, Product Type & End-Use
ReplyDeleteRed Rice Red market
Overview
At the beginning of a recently published report on the global Red Rice Red market, extensive analysis of the industry has been done with an insightful explanation. The overview has explained the potential of the market and the role of key players that have been portrayed in the information that revealed the applications and manufacturing technology required for the growth of the global Red Rice Red market.
Red Rice Red market
Как можно войти на прогрессивную платформу сайт гидры hydra на ПК
ReplyDeleteСхемы безымянных покупок на сайте hydra bot
ReplyDeleteНаправить деньги скрытно становится весьма сложно. Также придется учесть, что скрытые переводы проводят не исключительно жулики, но и рядовые пользователи. Вообразите, все же никто не решится платить большие деньги в качестве налогов от нечего делать, проведя выгодную . Преимущественно распространенной причиной для формирования анонимного платежа гидра сайт оригинал является работа в инете.
ReplyDeleteНа сайте гидра официальный hydparu zerkalo site посетители сумеют приобретать продукт поштучно, или крупнооптовой партией. Отыскать желаемый продукт довольно просто – разрешено сопоставить стоимость, или открыть рейтинг дилера. Умелые дилеры магазина ГидраUnion обладают определенным рейтингом, какой отображается всем юзерам маркетплейса. В этом месте есть возможность закупить особые субстанции, компьютерную технику или персональную информацию.
ReplyDeleteОбратитесь к форуму, на котором реально прочитать актуальные указания специалистов. Можно ли защититься от кибер атаки, можно учесть несколько практичных советов. Бывает большое множество вариантов сберечь свой комп от атаки злоумышленников. Множество советов, которые вы прочитаете на портале гидра сайт hydra9webe, абсолютно действительные.
ReplyDeleteЛишь только zoom видеоконференция предоставляет отличную телефонию и доступ к номеру в круглосуточном режиме. Оператор ТелКом предоставляет всем пользователям возможность включения IP номера. В Нижнем Новгороде использование виртуального номера от фирмы Тел Ком – это максимально оптимальное предложение на рынке.
ReplyDeleteВ интернет-сети находится действительно большое количество развлекательных ресурсов. Современные развлечения и живые взаимосвязи среди пользователей способствует создавать общества людей по определенным сферам. Также ссылка на гидру hydra ru zerkalo site – лучший из преимущественно известных сайтов, предоставляющий своим клиентам невероятный решение развлечений.
ReplyDeleteНа портале gidra магазин сайт вы сумеете отыскать вещи на свой вкус и цену. UnionГИДРА – это современный магазин, на каком можно закупить какие угодно изделия по самой низкой стоимости. На текущий момент 99 процентов определенных коммерческих сделок проводят в сети интернет. маркетплейс осуществляет свою деятельность на протяжении шести лет, и за этот промежуток времени смог охарактеризовать себя как выдающаяся торговая платформа.
ReplyDeleteС целью работы с партнерами вам в любом случае необходимо телефония через интернет. Не растрачивайте дополнительные суммы на монтаж городского телефона – используйте вирутальный номер! Пользователи в любой момент позвонят по определенным номерам телефона и осуществляют заказы, либо же определяют информацию по закупке. Не имея телефонного номера в настоящее время слишком сложно подготовить бизнес.
ReplyDeleteСкрытый вход на сайте hydra оригинальная – полезные товары по самой минимальной стоимости
ReplyDeleteИмеется возможность использовать запасную ссылку для организации приобретения продукции на маркете Hydra. Хозяева проекта Hydra ежесуточно обновляют действительные ссылки для входа на портал. Для доступа на как пополнить баланс на гидре требуется поставить особый веб браузер – TOP. Лишь только через браузер TOR новый посетитель может пройти в черный интернет.
ReplyDeleteVery awesome blog. Great stuff. Informative content. Very useful to many people. Keep up this good work.
ReplyDeleteData Science Certification in Hyderabad
Сеть интернет допускает возможности закачать немыслимое число файлов целиком бесплатно. С изменением web-технологий равнозначно модернизируют профессиональные привычки проходимцы, каковые работают на просторах интернета гидра вк. Заходя в интернет требуется наперед позаботиться о защищенности вашего девайса и находящейся на нём информации.
ReplyDeleteHydra выделяет всем покупателям великолепный ассортимент изделий по наиболее приличной цене от изготовителя. Любой желающий сможет верифицироваться на платформе и без проблем выполнить дело на необходимую сумму. Для постоянных юзеров гидра официальный сайт доступны дисконты. На портале представлено много производителей качественного товара.
ReplyDeleteБезликие заказы в маркетплейсе Hydra hydra ссылка tor зеркало
ReplyDeleteКибербезопасность относительно недавно является полноценным видом для обеспечения нормальной работы в Мировой сети. Собственно минимальный показатель понимания обеспечивает клиентам протекцию частных данных. Скажем, гидра зеркало ссылка hydra делится конкретными советами, как не стать заложником киберпреступников в инете.
ReplyDeleteС эволюцией кибернетических технологий равносильно модернизируют определенные навыки мошенники, каковые функционируют в сети интернет. Заходя в Мировую паутину требуется заблаговременно озадачиться о защите компьютерного девайса и находящейся на нем информации. Доступ к интернету приносит преимущества закачать невероятное количество файлов полностью на халяву http://yijiatang.com/home.php?mod=space&uid=111328.
ReplyDeleteМожно учесть, что наибольшее множество игроков подыскивают различные онлайн серверы. На просторах http://www.makeupdownunder.com/2012/03/day-to-night-eye-makeup-look.html клиенты отыщут массу игр, кроме этого серьезный портал для связи с единомышленниками вирт общества. Часто пользователи в интерактивной сети играют в виртуальные проекты.
ReplyDeleteНе стоит забывать, что неидентифицируемый вариант отправки платежных средств не даст полновесной безопасности сделки. Как правило не секрет, что в интернете имеется множество сайтов где можно транзакции денег анонимно. Основной регистр персональных виртуальных кошельков можно разыскать в магазине http://licey2kchr.ru/forum/user/218151-iliqyb. Каждый юзер, направляя деньги на скрытый виртуальный кошелек, не может далее подтвердить правоту своих транзакций.
ReplyDeleteСправочный интернет-портал http://kgti.kg/index.php?subaction=userinfo&user=awudyqu – это верный ассистент в борьбе с атаками кибер-преступников. Взломщики реализуют преступные деяния по различным причинам. В современном мире IT способов управления слишком элементарно стать мишенью атаки аферистов. Чаще всего хакеры используют юзеров на предмет материальной выгоды.
ReplyDeleteГадание разрешает угадать, что человека ждет в предстоящее время. Гадание на жену это попытка понять грядущие события непрерывно зачаровывал человека. Любой стремится просмотреть собственное грядущее и воспринимает конкретные варианты предсказания грядущего максимально достоверными.
ReplyDeleteСхема безымянных оплат на интернет-платформе гидра ссылка на сайт зеркало
ReplyDeleteРеально ли авторизоваться на сайт огромного маркета как зайти на гидра онион анонимно?
ReplyDeleteНа портале гидра официальный магазин функционирует надежная система охраны. Администрация проекта Гидра непрерывно наблюдает за беспрекословной реализацией проходящих контрактов. С целью обеспечения дополнительной защищенности есть возможность воспользоваться помощью гаранта. Только если поставщик не вышлет покет, то его магазин будет оперативно заблокирован на портале Hydra RU.
ReplyDeleteПравонарушители смогут войти на аппарат пользователя и получить онлайн-доступ к всей информации. Главным куском безопасности в интернете числится защита сетевого оборудования, с помощью которого производится вход в инет http://forum.baf.com.tw/home.php?mod=space&uid=229470. Действительно простой вариант взламывания – это внедрение вредоносных программ, допустим, трояны.
ReplyDeleteПровести персональный платеж в инете не так уж и просто, вместе с тем, фактически осуществимо. Работая удаленно, возьмем к примеру, фрилансер, различные исполнителиИмеется огромнейшее множество платежных систем, позволяющие перечислить различные суммы полностью без отслеживания http://bbs.kxunion.com/home.php?mod=space&uid=11561. огромное множество заказчиков сталкиваются с проблемой закрытого платежа денежных средств.
ReplyDeleteНа сайте http://fmcpe.com/index.php?subaction=userinfo&user=aluhabu также присутствует громаднейшее число увлекательных сведений – специализированные образовательные курсы, торенты и магазин товаров. Часть игр и сервисов на платной основе, тем не менее, существенное количество развлечений найдутся в виде демонстрационных данных. Платформа Hydra предоставляет шанс пользователям инета подбирать соратников по причине общения на определенную их тематику.
ReplyDeleteБлагодаря хорошей рекламе о Hydra RU узнают множество клиентов в интернете. Для реализации стопроцентного уровня надежности на http://wolfpacksurvival.com/foto/profile.php?uid=4406 надо реализовать определенные меры. Персональные сведения посетителей лишь только в кодированном варианте на виртуальном компе. ИТ разработчики интерактивного магазина озаботились о защите реальных юзеров.
ReplyDeleteСовременная площадка http://www.jikezhichang.com/space-uid-8354765.html даст шанс выкупить какой угодно товар невероятно быстро. Не включая безопасности при покупке юзеры в большинстве случаев думают затаить личную информацию. Беспроцентные транзакции в сети интернет являются первоочередной задачей для всякого интернет-магазина.
ReplyDeleteИспользуя многочисленную переадресовку вообще никто не может мониторить покупателя. Правильно применить для входа на портал ГидраРУ продвинутый протокол TOR. Заходите в систему портала http://mx05.yyisland.com/item/1391/ucp.php?mode=register всегда в режиме анонима. Массовая кодировка гарантирует наивысший показатель защиты для всех посетителей портала Hydra.
ReplyDeleteТут можно приобрести необходимые субстанции, мобильные гаджеты и важную информацию. Подобрать требуемый продукт более чем несложно – допускается сличить цену, либо открыть оценку дилера. На сайте Сhttp://mail.lawshare.tw/home.php?mod=space&uid=116492 юзеры могут купить товар поштучно, или значительными партиями. Умелые коммерсанты проекта Gidra имеют соответствующий ранг, он виден каждому клиенту сайта.
ReplyDeleteВеликое множество торговцев и приемлемые цены – вот важнейшие положительные причины, ввиду чего посетители закупляются на HydraЮнион. ГидраРУ является действительно популярным магазином, где продаются продукцию специального направления. Популярный маркетплейс http://bbs.sunmi.com/home.php?mod=space&uid=76509 размещен в скрытной части мировой сети.
ReplyDeleteКак быстро осуществить вход на сайт маркета Гидра в этом году https://www.tdseal.com/home.php?mod=space&uid=14546
ReplyDeleteHydraRU – это инновационный магазин, в каком можно получить любые товары по оптимально хорошей стоимости. На сайте http://bhidagt.hu/index.php/forum/user/3871-abecype вы имеете возможность найти гаджеты на любой вкус и цену. В наши дни 90 процентов определенных торговых договоренностей проводят в инете. Онлайн-магазин осуществляет профессиональную деятельность уже более 5 лет, и за столь длительный промежуток времени сумел охарактеризовать себя как крутая торговая платформа.
ReplyDeleteВон здесь http://hc-ld.ru/index.php?subaction=userinfo&user=ygaxy представлен действенный перечень продаваемого товара. На Hidra выставлено на удивление много фирменного товара, доступного всем пользователям интернет-сети. На платформе Гидра РУ не выйдет приобрести продукцию классическим приемом, а перевод принимают всего лишь на криптовалютные счета.
ReplyDeleteМаркетплейс ГидраРУ предоставляет каждому посетителю высочайший уровень анонимности при выполнении каждого договора. Воспользовавшись площадкой http://3asf.top/home.php?mod=space&uid=448317 покупатели получат достойный показатель анонимности. Нужно лишь пройти регистрацию на странице ГидраРУ, но твоя информация направится для хранения в шифрованном формате на виртуальном серваке.
ReplyDeleteИспользуйте сервис интерактивного сайта Hydra, или зеркалом сайта, если основной сервис перегружен. Благодаря интернет-магазину http://bbs.dtzchs.com/home.php?mod=space&uid=204360&do=profile любой желающий сможет провести безликую транзакцию. Отправляйте деньги в требуемом направлении без чрезмерных трат, таким образом не открывая индивидуальные данные.
ReplyDeleteПосле оплаты пользователю представят фотографию о точке, где потребуется взять приобретенный продукт. По адресу http://www.vytrvalost.com/diskuze/profile.php?id=4228 представлен каталог наиболее актуальных поставщиков торговой площадки. Первым делом придется найти нужный товар в одном из маркетплейсов HydraЮнион.
ReplyDeleteОтправляйте необходимую сумму в каком угодно направлении без ненужных процентов, в то же время не публикуя индивидуальные данные. Воспользуйтесь услугой интерактивного проекта «Гидра», или сайтом-зеркалом, если основная страница недоступна. Благодаря онлайн-магазину гидра биткоин тот или иной желающий может выполнить закрытую торговую операцию.
ReplyDeleteВеб-серфер для интернета TOR соединяется https://www.td-scs.ru/communication/forum/user/84742/ с заходом на огромное количество прокси-серверов. Благодаря интеллектуальной защите юзер может без особых усилий скачивать полезную информацию в Мировой сети. Присутствует огромнейшее количество защищенных веб-обзорщиков, что в режиме онлайна предотвращают эксперименты взлома вашего ПК или смартфона. Вычислить место входа в интернет через TOR полностью исключено.
ReplyDeleteДоступный каталог неидентифицируемых систем проплат есть возможность найти в маркетплейсе кошелек гидры. В основном не секрет, что в интернет сети находится множественное число проектов где есть способы транзакций электронных платежей скрытно. Не стоит забывать, что не верифицированный способ перевода денежных средств не дает стопроцентной защиты операции. Какой угодно клиент, переводя суммы на удаленный электронный адрес, не докажет правомерность этих манипуляций.
ReplyDeleteБлагодаря интернет-магазину hydraruzxpnew4af onion hydra хоть кто сможет произвести неидентифицируемую сделку. Переводите необходимые суммы в каком угодно направлении без дополнительных процентов, таким образом не публикуя индивидуальные данные. Используйте сервис интерактивного портала Hydra, или зеркалом сайта, если основной ресурс перегружен.
ReplyDeleteНа современных девайсах юзера, в основном, содержится основная информация о финансах, являющаяся целью злоумышленников. Отыскав инетресную информацию о владельце ПК, злодеи смогут использовать сведения для личных целей. Самую большую угрозу представляют вирусы для современных смартфонов. Обычно «угоняют» информацию о банковских картах юзера, либо логины от разных социальных сетей http://ustcbbs.com/home.php?mod=space&uid=194461.
ReplyDeleteмаркетплейс торгует уже более 6 лет, и за такой отрезок времени сумел охарактеризовать себя как выдающаяся торговая площадка. На странице https://230news.com/space-uid-532.html вы имеете возможность обнаружить товары на свой вкус и сумму. На сегодняшний день 99 процентов конкретных коммерческих операций осуществляют в инете. Гидра – это крупнейший маркет, на каком можно получить потребные гаджеты по наиболее выгодной цене.
ReplyDeleteЗаполучить скрытность реально лишь только на персональной платформе http://parttime.com.tw/home.php?mod=space&uid=361751. Не во всех системах обязательно вписывать личные данные, стоит именно использовать прибыльную систему платежей. Наиболее крупных виртуальные кошельки требуют необходимой освидетельствования пользователей.
ReplyDeleteСогласитесь, все же никто не хочет заплатить серьезные денежки в качестве налогов за глаза, проводя удачную . Наиболее распространенной причиной для осуществления закрытого счета гидра hydra ru zerkalo site является подработка в сети. Также необходимо учитывать, что незамеченные оплаты применяют не именно жулики, но и обыкновенные клиенты. Перевести требуемые суммы без верификации стало очень сложно.
ReplyDeleteОбновить баланс элементарно можно в личном аккаунте пользователя после активации. Для скрытой сделки продукта обычно используют криптовалюты. Для перевода рекомендуется применять биток и эфир. Оплата пакетов на портале hydra осуществляется в обязательном порядке в виде виртуального перевода. Криптографическая валюта – это самый надежный порядок провести покупку на Hydra.
ReplyDeleteОбеспечить доступ к дебетовым счетам пользователя для опытного кибер-мошенника элементарно. Применяйте только лишь http://fddxbvx.vidown.cn/bbs/home.php?mod=space&uid=423554 для регистрации на главный проект Hydra. Генеральным заданием злодеев значится интернет-атака рабочего компьютера. Во время нападения мошенников пользователь даже не разгадает, что на персональном ПК установлен сторонний софт.
ReplyDeleteПодтвердить честность продавца можно по комментариям на платформе https://krasko-pult.ru/forum/user/20008/. Масса грамотных поставщиков реализуют свои посылки в любой регион страны. Для проведения операции пользователю достаточно верифицироваться на основном сайте. Войти на платформу Hydra просто посредством какого угодно планшета, либо домашнего компьютера.
ReplyDeleteНа форуме ссылка на гидру hydra ru zerkalo site действует дополнительная система охраны. Если только реализатор не направит посылку, то его аккаунт будет оперативно ликвидирован на портале ГидраРУ. В интересах предоставления вспомогательной надежности нужно воспользоваться помощью гаранта. Администрация маркетплейса Hydra RU без устали поглядывает за точной реализацией проходящих операций.
ReplyDeleteЛюбой пользователь получит Гидра объективную защиту от администрации проекта. Средства при покупке направляют на временный счет маркетплейса, а после приема товаров – передаются собственнику. Купить требуемый продукт на HydraRU допустимо при помощи электронных денег или криптовалют. При расчете за товары https://weidiankoudai.com/home.php?mod=space&uid=45377, в большинстве случаев, берут электронные платежи.
ReplyDeleteВ наши дни представлено невероятное число цифровых кошельков. Особо простой порядок незамеченного выплаты электронных платежей – это применить http://uhome.haier.net/acbizbbs/home.php?mod=space&uid=623983. Перевести сумму денег определенному пользователю или любой фирме очень просто всевозможными методами.
ReplyDeleteВо время оплаты товаров гидра сайт hydra9webe com, как правило, используются виртуальный деньги. Виртуальные деньги при сделке направляют на временный счет продавца, а после получения продуктов – возвращаются собственнику. Каждый клиент получит HydraRU 100% защиту от собственников сайта. Заплатить за какой угодно товар на Hydra возможно при помощи электронных кошельков или биткойнов.
ReplyDeleteДля засекреченной операции пакета как правило используют криптовалюты. Обновить баланс легко можно в личном кабинете пользователя по завершению верификации. Плата за пакет на сайте http://my-beautysalon.de/index.php?subaction=userinfo&user=isujejo выполняется только в виде онлайн перевода. Криптовалюта – это самый надежный метод сделать покупку на Гидра. Для пересылки возможно применять биток или эфириум.
ReplyDeleteПрименяйте http://forum.l2fire.ru/index.php?/user/30993-omyfuwes/ чтобы войти на официальный проект Hydra. Открыть доступ к банковским карточкам пользователя для опытнейшего мошенника легко. Первой целью мошенников есть атака домашнего компьютера. В случае интернет атаки юзер вообще не определит, что на личном компьютере поселился сторонний программный код.
ReplyDeleteВысококвалифицированные торговцы проекта Hydra имеют определенный ранг, он виден каждому клиенту маркета. Приобрести нужный товар максимально несложно – возможно сравнить цену, либо просмотреть оценки дилеров. На форуме http://bhm.com.ua/index.php?subaction=userinfo&user=ajefe пользователи имеют возможность приобретать продукцию отдельной единицей, либо большой партией. Здесь есть возможность купить любые вещества, мобильные гаджеты и персональную информацию.
ReplyDeleteДопускается применять зеркалку для организации покупок на маркете Hydra RU. Лишь только при помощи браузера TOP какой угодно покупатель имеет возможность войти в даркнет. Администраторы маркетплейса UnionГИДРА постоянно обновляют своевременные адреса для авторизации на портал. Для верификации на гидра официальная ссылка приходится поставить специализированный веб браузер – TOR.
ReplyDeleteТолько крупных электронные кошельки потребуют стопроцентной идентификации участника. Не на каждом шагу понадобится оформлять персональные данные, стоит только использовать положительную платежную систему. Получить иммунитет идентификации получится всего лишь на особой платформе http://tstc.gxshw.shop/home.php?mod=space&uid=66809&do=profile.
ReplyDeletebest facial cleansers for combination skin
ReplyDeleteОтправляйте денежки в нужном направлении без чрезмерных трат, в то же время не демонстрируя индивидуальные данные. Воспользуйтесь услугой виртуального проекта «Гидра», а также сайтом-зеркалом, если основная страница загружена. В следствии работы интернет-магазина гидра ссылка 2022 кто угодно сможет осуществить скрытную транзакцию.
ReplyDeleteОтыскивая в интернет-сети особые продукты, человек по результату столкнется с проектом ГидраРУ. В глобальной паутине ну очень много выгодных магазинчиков. Наиболее добротный интерактивный магазин в интернете образовался на портале платформа гидра 2022. Большое число пользователей магазина требуют скупляться абсолютно анонимно.
ReplyDeleteЗащита данных теперь является специальным типом для гарантии нормальной деятельности в Глобальной сети. Так например, гидра интернет магазин 2022 делится детальнейшими указаниями, затем чтобы не стать мишенью преступников в инете. Собственно определенный показатель навыков даст юзеру сохраненность персональной информации.
ReplyDeleteМножество пользователей судят, что гарантировать 100% защиту в инете слишком тяжело, однако это является серьезным предрассудком. TOR – лучший веб-обозреватель, какой рекомендуется применять для просмотра информации в сети интернет. Актуальное ПО гидра через тор Пустошка даст своевременную охрану от злоумышленников.
ReplyDeleteПринять закрытый платеж в инете довольно сложно, но в то же время, вполне осуществимо. большинство сталкиваются с проблемой персонального платежа денежных единиц. Присутствует значительное количество сайтов, позволяющие направить средства полностью анонимно гидра санкт петербург 2022. Удаленная работа, к примеру, фрилансер, различные пользователи
ReplyDeleteКомпании, что дают интернет сообщение, в основном имеют в своих машинах специальную защиту от атак преступников, детальный список реально встретить на гидра сайт официальный вход. Создавать хорошую оборону персонального компьютера необходимо с поиска авторитетного хостинг-провайдера. Современные фаерволы – наилучшая защита от атаки злоумышленников в рабочую интерактивную сеть.
ReplyDeleteДля первого раза требуется отобрать надлежащий товар в одном из маркетов HydraЮнион. Проведя оплату человеку представят фотографию о месте, где нужно взять оформленный пакет. По ссылке http://kramday.com/photos/profile.php?uid=69173 представлен рейтинг наиболее проверенных торговцев платформы.
ReplyDeleteЗаполучить незаметность возможно лишь на специальной платформе gidra магазин сайт. Только старые виртуальные кошельки требуют полноценной подтверждения участников. Не в каждой электронной системе необходимо показывать персональные данные, стоит именно отыскать положительную платежную систему.
ReplyDeleteАнонимность при закупке криптовалютными денежными средствами гидра анаболик Невель
ReplyDeleteВиртуальные деньги зачисляются в основном кабинете покупателя. Пополнение баланса любого пользователя проводится персонально. Для закупа на tor gidra Шумиха применяют какие угодно виды виртуальных денег. На Hydra принимают выплаты Киви и даже пополнением на смартфон. Наиболее важным видом проплат сегодня считается токены.
ReplyDeleteКак авторизироваться на страницу крупного проекта ГидраРУ защищенно гидра рынок Астрахань
ReplyDeleteВсевозможные комплектующие и даже специализированный софт правильно заказать удаленно. Молодые клиенты закупают практически все товары дистанционно. Имеется конкретная продукция, закупить какую реально лишь онлайн. На странице https://store.hydraclubbioknikok.com в наличии обширный выбор продукции на твой вкус.
ReplyDeleteМожно ли авторизироваться на портал новейшего интернет-магазина Гидра защищенно гидра на русском языке Одинцово
ReplyDeleteНа сайте https://onion.www-hyrda.com вы сможете найти гаджеты на любой вкус и бюджет. ЮнионHYDRA – это новейший виртуальный маркет, в котором допускается выкупить требуемые продукты по самой приемлемой стоимости. Магазин занимается продажами уже более шести лет, и за столь долгий отрезок времени сумел проявить себя в качестве выдающейся торговой платформы. В наши дни 90 процентов конкретных коммерческих сделок заключают в интернете.
ReplyDeleteСтавить проверенную охрану своего ПК необходимо с поиска авторитетного интернет-провайдера. Предприятия, которые предоставляют услуги интернета, давненьки организовывают в компьютерных аппаратах мощную защиту от кибер атак, подробный список достаточно глянуть на gidra zerkala24 site 2022. Современные брандмауэры – наилучшая охрана от проникновения кибер-преступников в домашнюю интерактивную сеть.
ReplyDeleteПрисутствует огромнейшее число сайтов, позволяющих перечислять любые суммы совсем скрытно гидра тор официальный сайт онион Иваново. большое число пользователей сталкиваются с проблемой скрытного платежа средств. Удаленная работа, как пример, фрилансером, различные исполнителиПровести скрытый перевод в сети тяжело, но в то же время, весьма реально.
ReplyDeleteПодбирайте полюбившийся вариант развлечений в глобальной паутине на собственный манер. Любой желающий имеет возможность прийти на форум или портал развлекательного веб-сайта предзаказ на гидре Юрьев-Польский. С усовершенствованием ИТ методик в сети интернет есть значительное число игровых сайтов.
ReplyDeleteПриукрашают стены и полы керамогранитом по большей части ввиду её практических свойств. Если вы решили купить плитку в магазине Real Gres, необходимо просто просмотреть официальный сайт производителя. Ровная и гладкая поверхность довольно просто вытирается. Всякий посетитель, приобретая кафель в онлайн-магазине плитка valentia, получает действительно качественный товар.
ReplyDeleteЗалогиниться на https://store.hydraclubbioknikok.com очень просто используя уникальный браузер ТОR. Интеллектуальная маршрутизация даст возможность логиниться на портал быстро и анонимно. Для высокоскоростного соединения с виртуальным сервером проекта потребуется хороший ВПН. Для надежности разрешено активировать невидимку при регистрации на портал HydraRU.
ReplyDeleteВостребованный интернет-магазин https://web.xn--hydrclubbioknikokex-tub.com располагается в темной сфере глобальной паутины. Масса реализаторов и приемлемые цены – это основные положительные моменты, за счет чего клиенты скупляются на HydraRU. Гидра является по-настоящему востребованным интернет-сайтом, предлагающий вещи индивидуального направления.
ReplyDeleteОтправляйте необходимую сумму в нужном направлении без ненужных процентов, в то же время не показывая паспортные данные. За счет онлайн-магазина ссылка com гидры Алатырь любой пользователь сумеет сделать неидентифицируемую сделку. Воспользуйтесь услугой интерактивного портала Hydra, а также зеркалом сайта, если основной сайт загружен.
ReplyDeleteВерификация пользователей гидра обход Тверь в инете потребна для предотвращения надзорными органами противоправных действий. Анонимности в инете давно нет в том виде, как бывало, возьмем например, десятилетие тому назад. Жулики смогут оформить незаконные действия с деньгами клиентов.
ReplyDeleteЛюбой человек, направляя денежные средства на удаленный электронный адрес, не может в дальнейшем доказать правомерность этих переводов. Ни для кого не скрывают, что в интернете расположено тьма сайтов где возможно вывода электронных платежей без регистрации. Не нужно забывать, что неидентифицируемый способ транзакции денег не дает настоящей защиты соглашения. Главный список скрытых электронных кошельков возможно определить в маркетплейсе гидра магазин тор 2022.
ReplyDeleteЗаходите в сеть маркетплейса гидра анонимные покупки всегда в режиме анонимно. Рационально использовать для регистрации на форуме HydraRU продвинутый браузер ТОР. В результате постоянной переадресовки никто в мире не может проверить посетителя. Бесконечное шифрование гарантирует фундаментальный показатель защищенности для постоянных пользователей проекта HydraRU.
ReplyDeleteОтличный магазин практичных вещей гидра зеркало официальный 2022
ReplyDeleteПроцедура покупки в маркетплейсе http://www.realestateportal.org/users.php?mode=profile&uid=86733 устанавливается на положительных оценках официальных реализаторов. После проведения качественной операции пользователь выставляет продавцу положительную оценку, что для сторонних юзеров будет значить мотивом для осуществления последующих сделок. При назревании сложностей вы сможете обратиться к руководству ресурса «Гидра» для разрешения конкретных проблем, здесь юзеру конечно поддержат.
ReplyDeleteДобавленные зеркалки для входа в систему Гиды непрерывно меняются. Введенные имена надежно содержатся на частном прокси-сервере. Посетить зеркало сможет, как новый посетитель, и уже верифицированный пользователь. С точки зрения отдельной специфики портала http://www.oasq.com/home.php?mod=space&uid=1678277&do=profile, зайти в него можно за счет зеркала.
ReplyDeleteВерифицироваться на странице Hydra можно с использованием любого коммуникатора, или ноута. Целый ряд ответственных реализаторов реализуют свои продукты по всей территории Российской Федерации. Проверить ответственность магазина возможно по оценкам на платформе https://market.hydraclubbioknikoke.com. Для совершения операции пользователю нужно логиниться на официальном портале.
ReplyDeleteАккуратно находите продукцию, сопоставив цены в разных интернет-магазинах площадки UnionГИДРА. Для спокойствия юзеров функционирует постоянная поддержка. Конечно взгляните отзывы торговца, свежий список размещен по ссылке http://tznet.cn/home.php?mod=space&uid=207147&do=profile. Хозяева проекта непрерывно следят за соблюдением операций реализации в магазине.
ReplyDeleteВ наши дни 99 процентов определенных торговых договоров происходят в интернете. На портале правильная ссылка на hydra вы можете отыскать гаджеты на персональный вкус и сумму. HydraRU – это современный интернет-магазин, на котором есть возможность купить потребные вещи по оптимально приемлемой цене. маркетплейс торгует уже более 5 лет, и за столь многолетний период умудрился охарактеризовать себя как идеальная торговая платформа. Передать деньги нужному человеку или доверенной компании очень просто какими угодно методами. В настоящее время есть немыслимое число виртуальных кошельков. Самый легкий метод персонального перевода электронных платежей – это использовать http://www.speedyspares.com/forum/member.php?action=profile&uid=57781.
ReplyDeleteСамый крупный айти маркетплейс в интернете располагается на портале http://diakov.net/index.php?subaction=userinfo&user=oloseb. Отыскивая в интернете редкие товары, человек все равно сталкивается с платформой ГидраРУ. Большое количество клиентов маркетплейсов выбирают скупляться совершенно безопасно. В глобальной сети довольно огромное количество выгодных магазинов.
ReplyDeleteВыбирайте интересующий способ проведения досуга в интернет-сети на всякий вкус. В итоге совершенствования компьютерных технологий в сети интернет образовалось немыслимое множество интересных проектов. Каждый клиент сможет зайти на форум или портал развлекательного сайта ссылка на гидру онион hydra9webe.
ReplyDeleteВ настоящее время 99 процентов определенных торговых операций происходят в сети интернет. маркетплейс функционирует уже более шести лет, и за такой период смог проявить себя как лучшая торговая платформа. Гидра – это большой магазин, в котором доступно выкупить требуемые товары по действительно хорошей цене. На портале http://o4ooo.com/flowers/home.php?mod=space&uid=218781 вы можете найти вещи на свой вкус и сумму.
ReplyDeleteВозможно ли спасти себя от кибернетической атаки, рассмотрим небольшое количество адекватных рекомендаций. Огромное число советов, какие вы прочитаете на портале ссылка на гидру через тор, абсолютно актуальные. Обратитесь к форуму, на котором можно получить практичные советы специалистов. Имеется великое количество методов спасти свой комп от кибер атаки.
ReplyDeleteВ случае образования споров вы можете написать к руководству маркетплейса «Гидра» в целях разрешения разнообразных задач, в этом случае покупателю без сомнения поддержат. Порядок покупок в онлайн-магазине http://naszaswietlica.dwr.pl/profile.php?lookup=9915 строится на положительной оценке авторизированных реализаторов. При осуществлении положительной операции пользователь делает реализатору положительную оценку, для остальных юзеров это значится аргументом для заключения последующих сделок.
ReplyDeleteБлагодаря усовершенствованию IT методик в интернет-сети образовалось громадное количество развлечений. Выбирайте нужный вариант развлечения в интерактивной сети на всякий вкус. Всякий желающий может посетить форум или портал развлекательного веб-сайта https gidra.
ReplyDeleteВ силу особой специфики сайта http://bbs.68d.ca/home.php?mod=space&uid=8535, осуществить вход на него возможно за счет зеркала. Дополнительные источники для верификации в системе ГидраРУ постоянно меняются. Вводимые имена надежно записаны на зашифрованном компьютере. Посетить зеркало имеет возможность, как новый пользователь, и уже зарегистрированный юзер.
ReplyDeleteДостаточно пройти авторизацию на портале ГидраРУ, и персональная информация направится на хранение в закодированном формате на виртуальном серваке. Портал ГидраРУ дает всем клиентам отличный уровень безопасности при осуществлении конкретной транзакции. При помощи сервиса зеркала гидра hydra9webe com Певек пользователи обретут максимальный показатель анонимности.
ReplyDeleteДля совершения покупки человеку придется зарегистрироваться на основной платформе. Большое множество грамотных торговцев отпускают свою продукцию в любом направлении России. Подтвердить честность реализатора реально по отзывам на странице гидра обменник. Войти на портал Hydra RU возможно с использованием какого угодно коммуникатора, или стационарного компа.
ReplyDeleteОхрана данных давно выделяется узконаправленным типом для гарантии нормальной функциональности в интернете. В частности, http://www.wisvia.com/forum/home.php?mod=space&uid=36032 показывает конкретные алгоритмы, затем чтоб не стать мишенью мошенников в интернете. Только лишь определенный уровень представления дает пользователям протекцию персональных данных.
ReplyDeleteБезопасная покупка происходит исключительно в сети даркнет. Покупателю нет нужды подвергать себя убыткам, проводя сделку с реализатором товара. Множество пользователей догадываются о проекте UnionГИДРА, хотя зайти на него очень хитро. Какая угодно сделка на тор браузер гидра hydra ru zerkalo site обеспечит заказчикам отличную степень защиты.
ReplyDeleteПереведя деньги покупателю направят координаты о положении, где требуется взять оплаченный продукт. По ссылке http://ottomotive.pl/kunena/digital-ecu-cheater-i/875-hydra указан перечень максимально популярных торговцев платформы. Для первого раза надо отобрать нужный товар в любом из маркетплейсов Хидра.
ReplyDeleteТОР – наилучший браузер, который нужно применять для просмотра данных в инете. Актуальное ПО http://club.threebit.cn/space-uid-5347.html обеспечивает своевременную охрану от злоумышленников. Различные юзеры думают, что получить сто процентную защиту в интернет сети не выйдет, вот только это является серьезным предрассудком.
ReplyDeleteКакой угодно клиент, переводя денежные средства на скрытый электронный адрес, не подтвердит законность таких переводов. В основном не скрывают, что в интернете присутствует сколько угодно проектов где есть шансы вывода денежных средств анонимно. Полноценный каталог закрытых систем оплат возможно разыскать в маркетплейсе https://store.hydraclubbioknikok.com. Не стоит забывать, что не верифицированный вариант вывода денежек не дает полноценной безопасности операции.
ReplyDeleteКрупный игровой сайт для отдыха в сети интернет – Гидра https://official.xn--hydraclubboknkokex7-u1bd.com
ReplyDeleteНи для кого не секрет, что в сети интернет есть море сайтов где возможно перевода электронных платежей без регистрации. Всякий клиент, переведя денежки на не верифицированный виртуальный кошелек, не сможет позже подтвердить законность таких переводов. Полноценный каталог неидентифицируемых систем транзакций есть возможность подобрать на сайте гидра телеграм. Стоит понимать, что скрытый способ транзакции денежных средств не даст стопроцентной защиты сделки.
ReplyDeleteHydra – прогрессивный сайт развлечений https://market.hydraclubbioknikoke.com
ReplyDelete